Here’s a fun way to start a Monday morning: Your mobile app is a vault, and mobile threat detection is the only thing standing between your users and attackers who just got handed the combination to anyone with a laptop and a free afternoon.
That’s the uncomfortable truth about mobile security that most engineering teams avoid until it’s too late. Unlike a web application safely tucked behind a browser’s sandboxing protections, your iOS or Android binary sits directly on devices you don’t own, can’t control, and have no visibility into. The moment someone downloads your APK, they hold your API routes, your business logic, and sometimes your hardcoded secrets in their hands. They can decompile it, instrument it with Frida, and build automated botnets that mimic legitimate users so convincingly that your WAF waves them right through.
Mobile threat detection isn’t a feature you bolt on after launch. It’s an architectural decision that determines whether your platform survives contact with real adversaries.
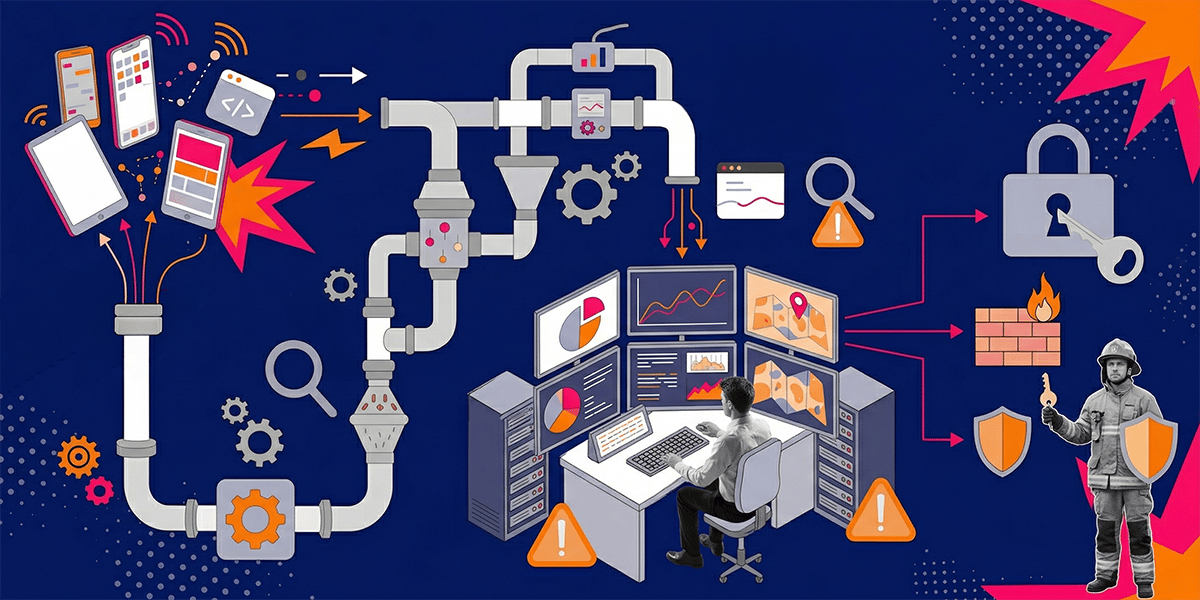
This guide walks you through building comprehensive mobile threat detection systems—from the telemetry signals that actually matter, to edge protection architecture, GDPR-compliant monitoring, and the continuous defense pipelines that keep your defenses sharp as threats evolve.
Whether you’re a CTO at a fintech startup, a DevSecOps lead protecting an e-commerce platform, or a mobile security architect tired of playing whack-a-mole with scrapers—this is the blueprint.
Ready to protect your mobile infrastructure properly? Schedule a free consultation with us at Iterators to assess your current security posture and build a defense strategy tailored to your platform.
Why Mobile Apps Are Prime Targets for Automated Attacks
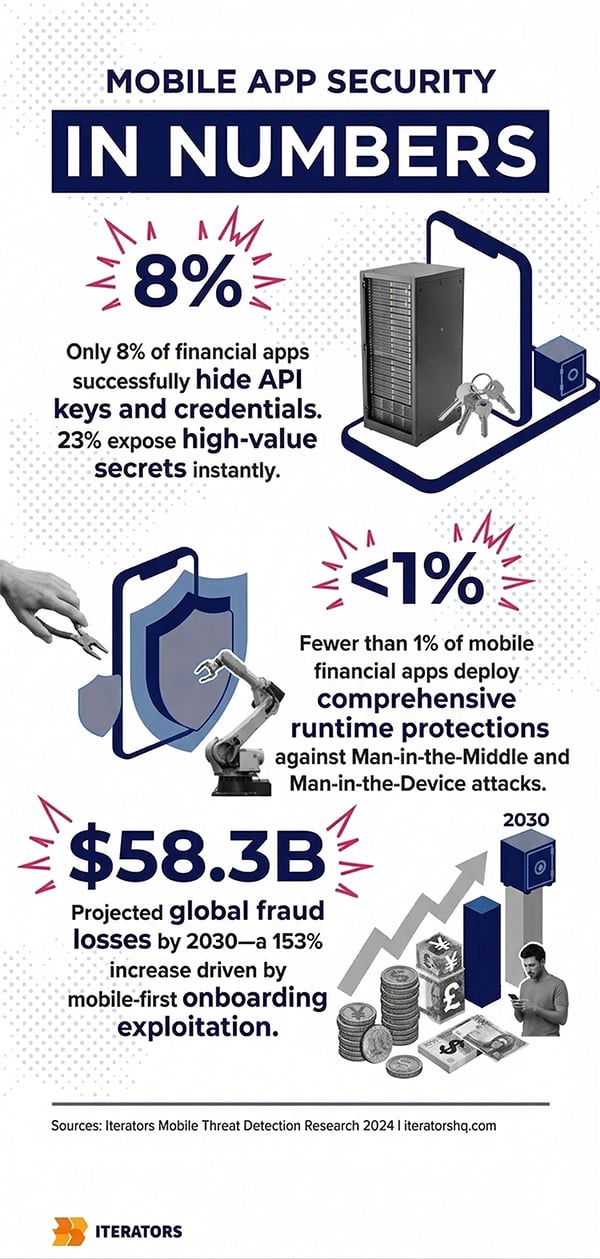
Let’s start with the uncomfortable statistics.
Only 8% of analyzed financial applications successfully conceal their secrets from immediate static extraction. Twenty-three percent immediately expose high-value secrets—private payment gateway keys, backend authentication tokens, the works—to anyone willing to spend thirty minutes with a decompiler.
That’s not a niche problem. That’s the industry baseline.
The Mobile Threat Detection Landscape Has Industrialized
The attack vectors targeting mobile applications have matured beyond what most security teams are prepared to handle. Reverse engineering tools that previously required deep assembly-level expertise now feature point-and-click interfaces. Frida, Xposed, and similar dynamic instrumentation frameworks let attackers hook into your application’s runtime processes, intercept TLS keys, bypass biometric prompts, and clone your application logic for redistribution.
The modern threat actor isn’t some lone genius in a hoodie. They’re running industrialized operations:
- Credential stuffing at scale: Automated scripts that cycle through leaked username/password combinations against your login endpoints, running across thousands of residential proxy IPs to avoid rate limiting
- API scraping: Bots that systematically harvest your product catalog, pricing data, or user-generated content—often to feed competitor platforms
- Synthetic identity fraud: AI-generated identities assembled from fragmented stolen data, used to open fraudulent accounts through mobile-first onboarding flows
- Surge pricing manipulation: Bots that artificially trigger demand signals in on-demand platforms to exploit algorithmic pricing
- Replay attacks: Captured valid API requests retransmitted at scale to brute-force accounts or manipulate in-app economies
Less than 1% of mobile financial applications evaluated in recent industry reports deployed comprehensive runtime protections capable of defending against both Man-in-the-Middle and Man-in-the-Device manipulations. That’s a staggering gap between the sophistication of attacks and the maturity of defenses.
The Cost of Getting Mobile Threat Detection Wrong
The financial implications are catastrophic. Global fraud losses impacting financial institutions are projected to reach $58.3 billion by 2030—a 153% increase—driven largely by synthetic identity fraud exploiting mobile-first onboarding flows. Cumulative global losses to online payment fraud between 2023 and 2027 are expected to exceed $343 billion.
And it’s not just direct financial theft. A major API exposure incident can result in the scraping of millions of user records. GDPR fines for such negligence can total up to 4% of global annual revenue. The reputational damage compounds everything.
The average cost of a U.S. data breach now exceeds $10 million. Professional mobile penetration testing costs a fraction of that—yielding an estimated 51,000% ROI for preventative security investments. The math is not complicated.
What Telemetry Actually Matters for Mobile Threat Detection
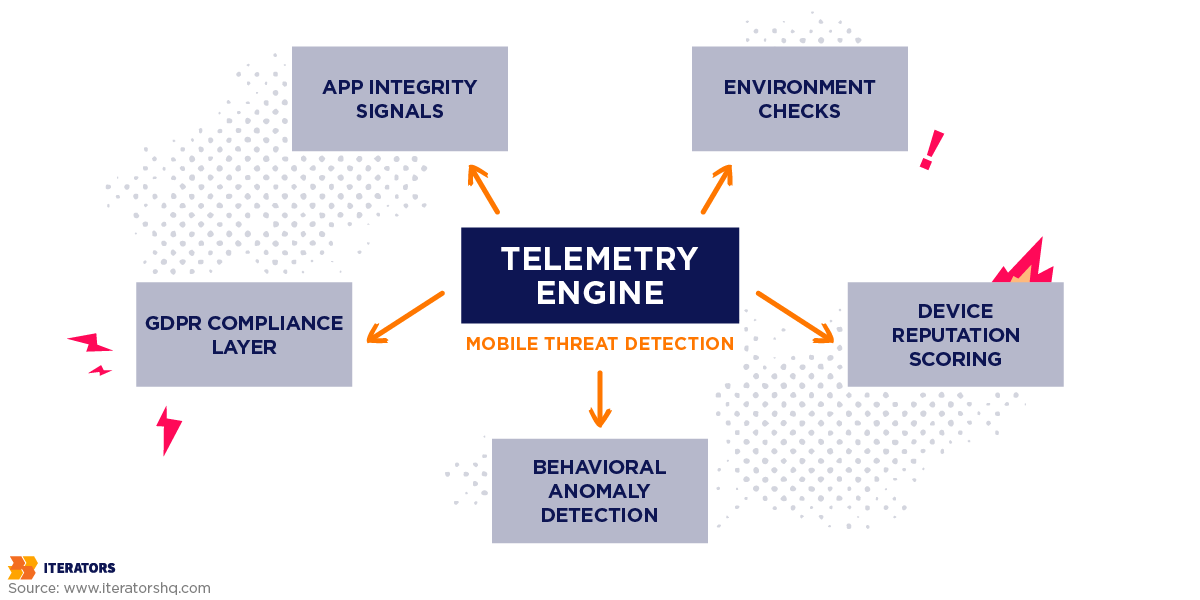
Here’s where most security guides go wrong: they list threats without telling you what signals to actually collect. So let’s be specific.
The foundation of effective mobile threat detection is acquiring high-fidelity telemetry directly from the runtime environment. Not network logs. Not IP reputation scores. The actual state of the device and application executing your code.
There are four categories of signals that matter:
App Integrity Signals and Runtime Validation in Mobile Threat Detection
App integrity signals answer the most fundamental question in mobile security: Is this the application you actually distributed, or has someone tampered with it?
When an attacker reverse engineers your application, modifies the business logic, and recompiles it, the cryptographic signature of the binary changes. Your mobile threat detection system needs to catch that.
The mechanism is cryptographic attestation. During execution, the application generates a signed payload within a secure hardware enclave—the Trusted Execution Environment on Android, the Secure Enclave on iOS. This payload certifies that the binary matches the version officially distributed via the app store.
Both major platforms provide native attestation APIs:
- Google Play Integrity API: Replaced SafetyNet in 2023. Provides verdict tokens indicating whether the app was installed from the Play Store, whether the device passes basic integrity checks, and the device’s certification status. The limitation is that it requires a network call to Google’s servers, introducing latency and a dependency on Google’s infrastructure.
- Apple App Attest: Available since iOS 14. Uses the device’s Secure Enclave to generate a cryptographic key pair bound to the specific app and device combination. Significantly harder to spoof than Play Integrity, but similarly locked into Apple’s ecosystem.
For organizations needing cross-platform consistency and more granular control, third-party attestation platforms like Approov or Guardsquare provide SDK-level solutions that work across both ecosystems with unified backend validation.
Environment Checks and Emulator Detection for Mobile Threat Detection
Validating the binary is insufficient if the operating system underneath it is compromised. Environmental telemetry focuses on the context in which your application is executing.
Root and jailbreak detection is the most fundamental environmental check. A rooted device has its operating system’s native sandboxing protections disabled, allowing malicious applications or background daemons to read memory spaces allocated to your application—effectively stealing session tokens or decryption keys.
Emulator detection is equally critical for mobile threat detection. Automated scraping operations and mass credential stuffing attacks rarely occur on physical hardware due to scaling costs. Attackers spin up thousands of Android emulators on server farms to orchestrate distributed attacks. Your telemetry needs to detect:
- Hypervisor signatures in system properties
- Mock location settings that indicate a simulated environment
- Absence of hardware sensors expected on physical devices
- Presence of dynamic instrumentation frameworks (Frida, Magisk)
- Debugger attachment indicators
The challenge is that sophisticated attackers know what checks you’re running and actively work to defeat them. This is why environment checks must be implemented at the compiler level—woven into the binary itself rather than added as detectable runtime calls.
Device Reputation Scoring in Mobile Threat Detection
Binary pass/fail signals are useful, but they miss the nuanced threat landscape. Device reputation scoring introduces continuous risk assessment across sessions.
By generating a persistent, cryptographically secure identifier for a specific hardware unit, your backend can track historical behavior across multiple sessions. If a device has been associated with a known botnet, has engaged in repeated failed login attempts indicative of credential stuffing, or exhibits impossible geographic velocity (logging in from New York and then London ten minutes later), its reputation score degrades.
A degraded reputation score triggers graduated responses:
- Minor degradation: Silently throttle request rates
- Moderate degradation: Require stepped-up authentication (biometric confirmation)
- Severe degradation: Block the session entirely and flag for SOC review
This layered approach—integrating with your multi-factor authentication infrastructure—creates dynamic friction that frustrates automated attacks while remaining invisible to legitimate users.
Behavioral Anomaly Detection in Mobile Threat Detection
Behavioral telemetry shifts focus from the device to the interaction patterns between client and API.
Human users interact with mobile applications in highly predictable sequences governed by the user interface flow. Someone checking out of an e-commerce application will view a cart, enter shipping details, process payment, and view a confirmation screen. They’ll spend time on each screen. They’ll scroll. They’ll occasionally go back.
Automated scripts, designed purely for speed and efficiency, often bypass intermediate steps—directly hitting payment or data extraction endpoints. They execute at machine speed. They never scroll. They never go back.
By capturing the sequential flow of API calls and training machine learning models on baseline behavioral norms, you can flag interactions that deviate violently from expected patterns before your backend database is ever queried.
Telemetry Signal Taxonomy
| Signal Type | What It Detects | Attack Vector Mitigated | Privacy Impact | Collection Method |
|---|---|---|---|---|
| App Integrity | Modified binaries, unauthorized repackaging | Cloned apps, logic bypassing, piracy | Minimal (No PII) | Cryptographic signature validation via secure hardware enclave |
| Environment Check | Root/Jailbreak, Emulators, Debuggers | Dynamic instrumentation, memory hooking, automated farms | Low (Hardware state only) | OS-level API queries and hypervisor footprint detection |
| Device Reputation | Historical abuse, geographic velocity, auth failure patterns | Credential stuffing, coordinated botnets | High (Requires anonymization) | Device fingerprinting with server-side scoring |
| Behavioral Anomalies | Impossible API state transitions, non-human interaction speeds | API scraping, bypass attacks, mass automation | Low (Focuses on API path, not user identity) | Markov chain probability matrices at the edge |
Building Mobile Threat Detection Observability Systems

Acquiring raw telemetry is the first step. The real challenge is building observability architecture that ingests, normalizes, and correlates massive volumes of runtime signals against backend traffic patterns without drowning your SOC team in false positives.
Identifying Scraping vs. Legitimate High-Volume Users
This is the question that trips up most security teams. A power user hammering your API is not the same as a scraper hammering your API—but the raw request counts can look identical.
The answer is path normalization combined with contextual volumetric baselines.
Modern edge platforms use unsupervised learning to automatically map your API attack surface. Through path normalization, the system collapses disparate parameterized endpoints into standardized variable paths. /api/user/123/profile and /api/user/456/profile both become /api/user/*/profile.
Once normalized, the system establishes unique volumetric baselines for every specific path. A GET /feed endpoint might naturally see 300 requests per minute from an active user scrolling a social application. A POST /reset-password endpoint should rarely exceed two requests per minute. Applying a global rate limit treats both endpoints identically—which is exactly wrong.
Context-aware observability engines flag anomalies based on the specific intent of the endpoint. This prevents the blunt-force application of rate limits that inevitably degrade the legitimate user experience while letting sophisticated scrapers sail through at just-below-threshold speeds.
Detecting Mass Automation and Replay Attacks
Sequential anomaly detection is the mechanism that catches automated traffic that knows your rate limits and respects them.
Advanced observability tools construct transition matrices using Markov Chains, mapping all possible API states and the statistical probability of moving from one state to another. If the system calculates that the probability of moving from Step A directly to Step C without passing through Step B is 0.001%, any traffic exhibiting that pattern is immediately classified as an outlier.
This methodology acts as SDK-less bot management. Because mobile applications enforce rigid UI sequences, any traffic that perfectly structures API payloads but fails to respect required sequential state transitions is definitively automated. The attacker has correctly reverse-engineered your API schema—but they’ve revealed themselves by ignoring the state machine that governs legitimate usage.
Correlating Mobile Runtime Signals with Backend Telemetry
The most dangerous blind spot in enterprise security architectures is the isolation of client-side telemetry from backend SIEM systems.
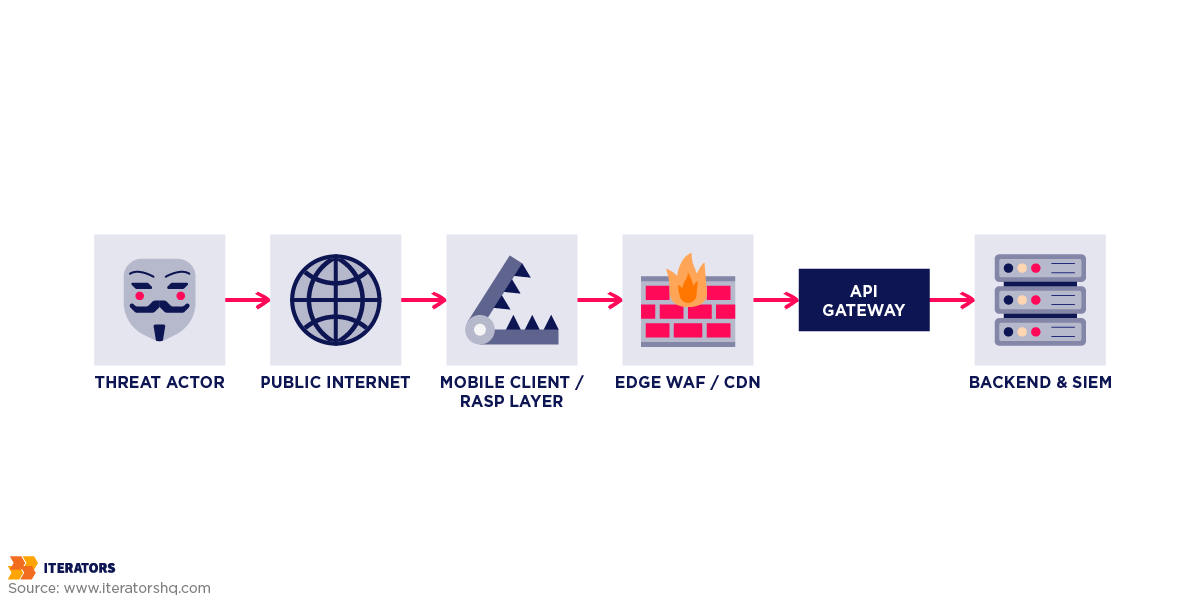
When a mobile client detects a rooted device or an injected Frida hooking framework via its RASP module, that event must not remain trapped on the device. The detection is useless if your API gateway doesn’t know about it.
Leading DevSecOps organizations deploy architectures where client-side signals are correlated with gateway telemetry in real time. If a device fails an attestation check, the mobile client transmits a signed failure token to the API gateway. The gateway drops all subsequent requests bearing that device’s session token.
The practical result: an attacker can successfully root their device and instrument your application, but the moment they attempt to communicate with your backend, the compromised device’s signature triggers an immediate block. Their investment in reverse engineering returns zero value.
Mobile Threat Detection Architecture
| Architectural Layer | Core Components | Primary Security Function | Threat Mitigation Focus |
|---|---|---|---|
| Mobile Client (Edge) | RASP, Native Attestation, Cryptographic Enclaves | Detects environment hostility, app tampering, executes local defense | Emulators, Repackaging, Memory Hooking |
| Edge Protection (CDN/WAF) | Cloudflare/Akamai, Markov Chain Engines, Path Normalization | Processes massive traffic volumes, enforces sequential logic, absorbs DDoS | Hyper-volumetric scraping, Mass Automation, DDoS |
| API Gateway & Backend | Rate Limiters, Token Validators, IAM | Validates attestation tokens, enforces RBAC, checks device reputation | Unauthorized Access, Credential Stuffing, Replay Attacks |
| Observability / SIEM | Data Lakehouse, Threat Dashboards, Automated Runbooks | Correlates cross-channel data, visualizes anomalies, updates rules | Long-term APTs, Coordinated multi-channel botnets |
The Role of WAF in Mobile Threat Detection and Defense

The Web Application Firewall represents the critical intermediary layer between the public internet and your backend databases. But traditional WAFs were engineered to protect web browsers—relying on IP reputation and regex signature matching to block known vulnerabilities like SQL injection or XSS. Mobile threat detection requires a fundamentally different approach.
Rate Limiting Strategies for Mobile Threat Detection
Static rate limiting—blocking an IP address that exceeds 100 requests per minute—is entirely ineffective against modern mobile threats. Mobile devices constantly transition between cellular towers and Wi-Fi networks, causing IP addresses to change continuously. Attackers distribute scraping operations across millions of residential proxy IPs so no single node triggers a static threshold.
Effective rate limiting for mobile threat detection must anchor to the device identifier or authenticated user session, not the IP address. Thresholds must be adaptive—automatically scaling based on contextual factors like promotional events or natural traffic surges.
The key architectural principle: your rate limiting logic should be smarter than your attackers’ threshold detection scripts. If they can probe your limits and stay just below them, your rate limiting is security theater.
Behavioral Analysis and Bot Mitigation for Mobile Security
Modern WAFs integrate with advanced bot management systems to evaluate the intent of traffic rather than just its volume. An API request can be evaluated against multiple behavioral signals simultaneously:
- TLS fingerprint analysis: Does the TLS handshake match the fingerprint expected from the claimed client (iOS 17, Android 14)? A Python scraping library’s TLS fingerprint looks nothing like a genuine mobile client, regardless of what the User-Agent string claims.
- HTTP header consistency: Real mobile clients send headers in predictable orders with specific values. Automated clients frequently send inconsistent header combinations that reveal their synthetic origin.
- Timing analysis: Human interactions have natural variance in timing. Machine interactions execute at consistent, inhuman speeds.
When a request perfectly matches the TLS fingerprint of a known Python scraping library despite claiming to be an iOS device, the WAF blocks the transaction before it ever reaches your application servers. This behavioral validation at the edge saves massive compute resources and prevents backend database load from automated abuse.
Edge Protection Platform Comparison
Choosing the right edge protection platform significantly impacts your defensive capabilities:
| WAF Provider | Core Mobile API Capabilities | Strategic Strengths | Best Fit |
|---|---|---|---|
| Cloudflare WAF | Unsupervised API discovery, Markov Chain sequential anomaly detection, robust free tier | Rapid deployment, accessible pricing, excellent for agile DevSecOps teams | Mobile-first startups needing immediate out-of-the-box API protection |
| Akamai | Deep enterprise bot management, advanced payload inspection, 2.5 exabytes processed annually | Highly customizable, extensive legacy integrations, dedicated managed services | Large-scale financial or enterprise environments requiring granular control |
| AWS WAF | Pay-as-you-go, Managed Rules via Marketplace, deep API automation for rule generation | Native AWS ecosystem integration, infrastructure-as-code management | Teams fully entrenched in AWS needing tight IAM integration |
Why Edge Protection Alone Isn’t Enough for Mobile Threat Detection
This is the architectural insight that separates mature security programs from checkbox compliance exercises.
“Edge protection without client attestation is like having a heavy vault door but giving the combination to anyone who asks nicely. You must correlate the cryptographic proof of application integrity generated on the device with the network-level behavioral analysis at your WAF. Only when these layers intersect do you achieve a zero-trust mobile architecture.”
— Lead Security Architect, Iterators
A WAF evaluates network-level traffic. It cannot inherently know if the mobile device originating the traffic is rooted or running a modified binary. Conversely, client-side app attestation cannot absorb a volumetric DDoS attack.
The defense-in-depth architecture requires all three layers working in concert:
- Attestation provides cryptographic proof that the client is legitimate
- WAF/Edge enforces behavioral and volumetric controls at scale
- Behavioral analysis catches sophisticated attackers who pass the first two checks but reveal themselves through interaction patterns
When attestation integrates with the WAF, the edge platform enforces a strict policy: drop all API requests that don’t contain a valid, cryptographically verified attestation token. This hybrid approach guarantees your backend only processes traffic from pristine, unmodified mobile clients.
Defense-in-Depth Coverage Analysis
| Security Control | Methodology | Speed | Implementation Complexity | Primary Weakness |
|---|---|---|---|---|
| Compiler-based RASP | Deep binary obfuscation and local runtime monitoring | High / Zero UX friction | High (Requires CI/CD build integration) | Cannot prevent network-level volumetric DDoS |
| Edge WAF Blocking | Network-level payload inspection and rate limiting | Blazing fast / Executed at CDN edge | Low to Medium (DNS routing) | Blind to client-side binary tampering or root status |
| Behavioral Analytics | Machine learning of API state transitions | High / Operates asynchronously | Medium (Requires ML training time) | Susceptible to false positives during major UX updates |
| App Attestation | Cryptographic signature validation via secure enclave | Slight latency (Token generation required) | Medium (Requires backend validation logic) | Native tools lock you into specific vendor ecosystems |
Designing GDPR-Friendly Mobile Threat Detection Telemetry

Aggressive mobile telemetry collection inherently collides with global privacy regulations. The GDPR definition of “Personal Data” is exceptionally broad—encompassing location information, cookies, and device identifiers if they can be linked directly or indirectly to an individual.
In 2026, regulatory enforcement has shifted from evaluating user-facing consent banners to examining the “technical truth” of backend data flows. Regulators use network monitoring tools to discover analytics SDKs firing before consent is granted. The fines are not hypothetical.
Article 25 of the GDPR mandates “Data Protection by Design and by Default.” Your mobile threat detection systems must minimize data collection from their inception—not as a retrofit.
Collecting Security Signals Without Personal Data
The key insight is this: security teams don’t need to know who is using a device. They only need to know if the device itself is exhibiting hostile behavior.
This reframing allows you to collect powerful security telemetry while staying firmly outside the scope of personal data processing.
Effective GDPR-compliant mobile security monitoring focuses on:
- Device behavioral patterns rather than device identity
- API interaction sequences rather than user journey mapping
- Environmental state signals rather than location or demographic data
- Aggregate anomaly scores rather than individual session records
The moment you link a behavioral pattern to a user identity, you’ve entered personal data territory. Keep those systems architecturally separate.
Double-Hashing and Cryptographic Anonymization
Basic pseudonymization is insufficient under GDPR because the original data can often be recreated. True anonymization requires mathematical irreversibility.
Advanced mobile threat detection platforms use a rigorous double-hashing and salting methodology:
- Device-side salting: When the mobile SDK generates or queries a hardware identifier, it does not transmit the raw string. The identifier is salted (combined with a randomized string) directly on the user’s device.
- First hash: The salted identifier is hashed locally using a secure cryptographic algorithm.
- Server-side salting: Upon reaching the backend, the platform appends a second, secret server-side salt.
- Second hash: The payload is hashed a second time.
This dual-layer transformation guarantees that neither the application developer nor the security vendor can reconstruct the original device identifier. Because the data is demonstrably irreversible, it’s legally reclassified outside the scope of “personal data”—allowing security teams to process behavioral anomalies and reputation scores globally without GDPR exposure.
Compliant systems also intentionally discard the exact identification date metadata, destroying the temporal correlation required for re-identification.
Data Retention and Deletion Policies
Even anonymized security logs shouldn’t be retained indefinitely. A compliant mobile threat detection architecture enforces automated data lifecycle policies:
- Real-time edge blocking data: Resides in memory, purged immediately after evaluation
- Short-term behavioral baselines: 30-day rolling window, automatically expired
- Aggregated threat intelligence: Further generalized before long-term storage (grouped by regional cohorts, not individual nodes)
- Incident records: Retained for the minimum period required for legal or compliance purposes, then automatically deleted
The automation is critical. Manual deletion processes fail. Build the expiration into the data architecture itself.
GDPR-Compliant Telemetry Decision Framework
Is this signal linkable to a specific individual?
├── YES → Can it be irreversibly anonymized before collection?
│ ├── YES → Apply double-hash + salt, collect anonymized signal
│ └── NO → Do not collect. Find alternative signal.
└── NO → Is it necessary for security function?
├── YES → Collect with defined retention period
└── NO → Do not collect. Minimize surface area.
Building Actionable Mobile Security Dashboards

The sheer volume of telemetry generated by mobile threat detection systems can easily result in alert fatigue. Security Operations Center analysts overwhelmed by false positives stop trusting the system—and that’s when real attacks slip through.
Effective dashboards abstract complex cryptographic and behavioral signals into unified risk scores that enable rapid decision-making.
Risk Scoring Methodologies
A robust mobile threat detection dashboard calculates an aggregate “Request Anomaly Score” for every transaction, weighting inputs from multiple signal vectors:
- Failed attestation check: High-weight negative signal (device is definitively compromised)
- Emulator detection: High-weight negative signal
- Geographic velocity anomaly: Medium-weight negative signal (could be VPN usage)
- Sequential API state violation: High-weight negative signal (definitively automated)
- Device reputation degradation: Graduated weight based on severity
- Behavioral timing anomaly: Medium-weight signal (requires corroboration)
The composite score determines the automated response tier. Analysts focus their attention on the small percentage of requests that score in ambiguous ranges—not the clear-cut blocks or clear-cut approvals.
When integrated with data lakehouses like Datadog or Splunk, these dashboards provide macroscopic visibility: geographic threat heatmaps identifying localized spikes in emulator usage, real-time API abuse trends segmented by endpoint, and trend analysis that reveals the evolution of attack patterns over time.
Integrating Mobile Threat Detection into CI/CD
The economic argument for shifting security left is undeniable. Discovering and remediating security flaws during development costs up to 60 times less than addressing the same vulnerabilities post-production.
Mobile threat detection must integrate directly into your CI/CD pipeline. The DevSecOps lifecycle for mobile security encompasses distinct phases:
Plan Phase Teams execute threat modeling exercises mapped to the OWASP Mobile Application Security Verification Standard (MASVS). They define baseline controls (MASVS-L1) for standard applications and rigorous defense-in-depth measures (MASVS-L2) for financial platforms. This is also where you define your telemetry collection strategy and privacy controls.
Build Phase Developers implement secure coding practices—explicitly avoiding hardcoded secrets, using environment-specific configuration management. The build pipeline automatically applies code hardening and obfuscation to the compiled binary. Every build produces a hardened artifact, not just your production releases.
Test Phase Every code commit triggers automated Static Application Security Testing (SAST) to uncover exposed keys and insecure configurations. Dynamic Application Security Testing (DAST) validates the binary against runtime manipulation in staging environments. This is also where you validate that your telemetry collection is functioning correctly and that your GDPR anonymization is working as designed.
Operate and Monitor Phase Real-time threat monitoring feeds telemetry back into the development loop. When mobile threat detection monitoring reveals that attackers are consistently targeting a specific endpoint, that signal feeds directly into the next sprint’s security backlog. Security becomes a continuous feedback loop, not a periodic audit.
This integration ensures that security testing is a concurrent enabler of release velocity, not a sequential bottleneck. The teams we work with at Iterators who implement this approach consistently report faster release cycles alongside improved security posture—because they’re catching issues during development rather than scrambling to patch production.
Mobile Threat Detection Implementation Checklist
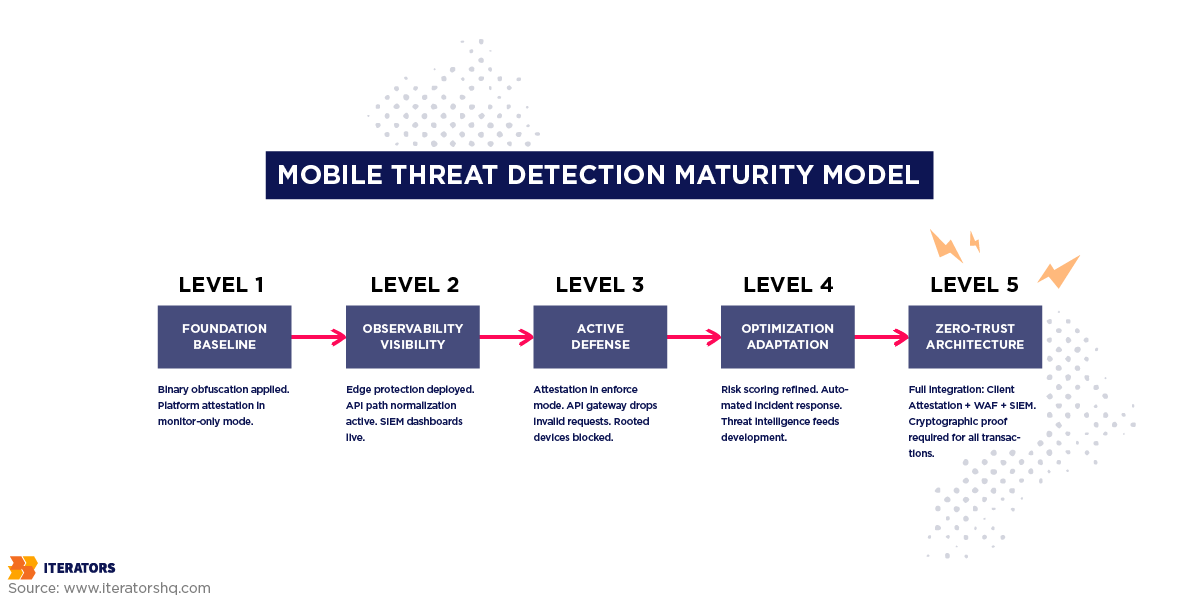
Transitioning from reactive to proactive mobile threat detection requires a phased, methodical approach. Attempting to deploy RASP, strict WAF rules, and behavioral anomaly detection simultaneously often results in critical disruption to legitimate user traffic.
A Phased Rollout Strategy
Phase 1: Foundation (Weeks 1-2)
Begin with baseline hygiene. Implement compiler-based code obfuscation (ProGuard/R8 for Android, standard Xcode settings for iOS) to strip cleartext strings from your binary. Integrate native platform attestation APIs in “monitor-only” mode to establish a baseline of tampered traffic without actively blocking users.
The monitor-only phase is critical. You need to understand your baseline before you start enforcing. How many of your users are on rooted devices for legitimate reasons (developers, power users)? What percentage of your traffic comes from emulators (often legitimate QA automation)? These baselines determine your enforcement thresholds.
Phase 2: Observability (Weeks 3-4)
Deploy edge protection tools to map your API attack surface. Use unsupervised learning to achieve path normalization and establish volumetric baselines for every critical endpoint. Route client-side telemetry to your SIEM infrastructure. Build your first dashboards. Start understanding what “normal” looks like for your application.
Phase 3: Active Defense (Weeks 5-6)
Transition attestation checks from “monitor” to “enforce.” Configure the API gateway to drop requests lacking valid cryptographic signatures. Implement sequential anomaly detection at the edge to mitigate scraping and mass automation. Start with your highest-value endpoints (authentication, payment processing, data export) before expanding to the full API surface.
Phase 4: Optimization (Ongoing)
Refine risk scoring methodologies using aggregated data lakehouse insights. Configure automated incident response playbooks—triggering forced biometric re-authentication for devices with degrading reputation scores, automatically updating WAF rules based on emerging threat signatures, feeding threat intelligence back into your development security backlog.
Avoiding Common Pitfalls
The App Wrapper Trap
The most pervasive pitfall in mobile security is over-reliance on “no-code” app wrappers or basic SDK integrations for runtime protection. App wrappers function by encasing the binary in a superficial layer of encryption and generic security checks. But because the wrapper logic is identical across thousands of different applications, an attacker who breaks the wrapper on one app instantly possesses the tools to break your app as well.
Genuine resilience requires compiler-based obfuscation and RASP solutions. These tools parse and model source code during the build process, weaving randomized security controls and arithmetic obfuscation directly into the application’s unique binary. This resets the clock for attackers—they must start reverse engineering entirely from scratch for every single release.
The iOS Complacency Trap
Implementing robust protections for Android while neglecting iOS—based on the dangerous misconception that the Apple ecosystem is inherently secure—leaves massive backdoors open. iOS devices can be jailbroken. iOS applications can be instrumented. The threat landscape is different, not absent.
The False Positive Spiral
Overly aggressive WAF rules trigger false positives that degrade the user experience. Users encounter blocks, file support tickets, abandon your platform. Security teams, overwhelmed by complaints, loosen the rules. Attackers notice and exploit the relaxed posture.
The solution is graduated enforcement. Start with monitoring, establish accurate baselines, enforce conservatively, and expand coverage incrementally as you validate that your rules are accurate.
The Siloed Detection Trap
Client-side detection that doesn’t feed backend systems is security theater. Backend detection that doesn’t incorporate client-side signals is blind. Build the correlation architecture from day one, even if you’re only collecting a handful of signals initially. The architecture is harder to retrofit than the signal collection.
Do’s and Don’ts of Mobile Threat Detection
| Do | Don’t |
|---|---|
| Anchor rate limiting to device identifiers, not IP addresses | Apply global rate limits without endpoint-specific baselines |
| Implement attestation in monitor mode before enforcement mode | Deploy enforcement without establishing baselines first |
| Correlate client-side signals with backend telemetry | Keep client-side and backend detection systems isolated |
| Use compiler-based obfuscation woven into the binary | Rely on superficial app wrappers that apply identical logic across all apps |
| Design GDPR compliance into telemetry architecture from day one | Retrofit privacy controls onto existing telemetry collection |
| Implement parity across iOS and Android | Treat iOS as inherently secure and skip protections |
| Build automated response playbooks | Rely on manual SOC intervention for all threat responses |
| Feed threat intelligence back into development sprints | Treat security as a periodic audit rather than a continuous loop |
Tools and Platform Recommendations for Mobile Threat Detection

The mobile threat detection ecosystem has matured significantly. Here’s an honest assessment of the major categories:
Mobile Attestation Platforms
- Google Play Integrity API: Best for Android-first applications. Tight ecosystem integration, no additional cost. Limitations include network dependency and Google’s control over verdict granularity.
- Apple App Attest: Best for iOS-first applications. Cryptographically robust using the Secure Enclave. Similarly ecosystem-locked.
- Approov / Guardsquare: Cross-platform solutions that provide unified attestation across iOS and Android with more granular control. Higher implementation complexity, but valuable for organizations needing consistent cross-platform security posture.
Edge Protection and WAF
- Cloudflare: Excellent starting point for most organizations. Strong API abuse detection capabilities, accessible pricing, rapid deployment. The Bot Management tier provides sophisticated behavioral analysis.
- Akamai: The enterprise choice for organizations with complex requirements and dedicated security teams. Significantly more expensive, but the customization depth is unmatched.
- AWS WAF: The pragmatic choice for AWS-native organizations. Sufficient for most use cases, deep IAM integration, infrastructure-as-code friendly.
SIEM and Observability
- Datadog: Strong mobile telemetry ingestion, excellent dashboarding, good ML-based anomaly detection. Pricing scales with data volume—can get expensive at scale.
- Splunk: The enterprise standard. Powerful query language, extensive integration ecosystem. Steep learning curve and licensing costs.
- ELK Stack (Elasticsearch, Logstash, Kibana): Open-source option with significant operational overhead. Cost-effective at scale if you have the engineering capacity to manage it.
The Future of Mobile Threat Detection
The generative AI frontier in mobile security is worth watching. AI-driven threat detection is moving from signature-based to behavioral-based approaches, with models that can identify novel attack patterns without prior exposure. The organizations building these capabilities into their security pipelines now will have significant advantages as the threat landscape continues to evolve.
Mobile threat intelligence from industry leaders like F5 Labs and Gartner’s security research provide valuable insights into emerging attack vectors and defensive strategies that should inform your mobile threat detection roadmap.
Conclusion: Building Resilient Mobile Threat Detection Systems
Mobile threat detection is not a product you buy and deploy. It’s an architectural discipline you build into every layer of your stack—from the cryptographic enclaves in your users’ devices to the behavioral analysis engines at your edge, through to the automated response playbooks in your SIEM.
The threat landscape has industrialized. Attackers are running automated operations at scale, exploiting the fundamental asymmetry of mobile security: you build one application, they have unlimited time to attack it. The only way to close that asymmetry is through continuous, layered defense that makes your application progressively more expensive to attack.
Start with your telemetry foundation. Understand what signals matter—app integrity, environmental context, device reputation, behavioral patterns. Build the observability infrastructure to collect and correlate those signals. Add edge protection that enforces behavioral controls at scale. Integrate attestation to provide cryptographic proof of client legitimacy. Design GDPR compliance into the architecture from day one, not as a retrofit.
Then wire it all into your CI/CD pipeline and treat security as a continuous feedback loop, not a periodic checkpoint.
The organizations that get this right don’t just avoid breaches. They build mobile platforms that their users can trust—and in an era where trust is the scarcest resource in consumer technology, that’s a genuine competitive advantage.
If you’re building a mobile platform that needs to survive contact with real adversaries, we’ve done this before. At Iterators, we’ve built security architectures for fintech platforms, on-demand services, and enterprise applications across multiple industries. The mobile development decisions you make today determine the security posture you’ll be defending tomorrow.
Schedule a free consultation with us to build a mobile threat detection strategy that protects your users, your data, and your reputation.
Frequently Asked Questions

What’s the difference between mobile and web threat detection?
Web threat detection operates within the standardized, sandboxed environment of a web browser, relying heavily on IP reputation, cookies, and HTTP headers. Mobile threat detection must account for compiled binaries executing on hostile, fragmented hardware. It requires cryptographic app attestation, root and jailbreak detection, and defense against dynamic instrumentation—factors completely irrelevant to web browser security. The client environment in mobile is fundamentally adversarial in ways that web environments are not.
How much does mobile threat detection cost to implement?
Costs vary significantly based on scale and architecture. Professional mobile penetration testing typically ranges from $20,000 to $35,000. Edge protection platforms like Cloudflare start with accessible pricing tiers and scale with traffic volume. The ROI calculation is straightforward: the average cost of a U.S. data breach exceeds $10 million, while proactive security programs cost a fraction of that. The estimated ROI of preventative mobile security investment is approximately 51,000%.
Can mobile threat detection work with GDPR compliance?
Yes, but it requires rigorous technical architecture from day one. GDPR compliance requires “Data Protection by Design.” Modern mobile threat detection achieves this through mathematical anonymization—device-side salting combined with server-side double-hashing—that guarantees device identifiers cannot be reverse-engineered or linked to personal identities. Security monitoring operates on anonymized behavioral signals, not personal data.
What are the best tools for mobile API protection?
A defense-in-depth approach requires a synthesis of tools. For edge protection and behavioral API anomaly detection, Cloudflare and Akamai are industry leaders. For compiler-based code hardening and RASP, solutions like Guardsquare provide deep binary protection. Unified attestation platforms like Approov bridge the gap between fragmented OS ecosystems. The right combination depends on your scale, budget, and existing infrastructure.
How do you prevent false positives in mobile security monitoring?
False positives are mitigated through context-aware observability and path normalization. Instead of applying global rate limits, advanced WAFs establish unique volumetric baselines for every API endpoint. Correlating client-side attestation failures with backend behavioral analytics ensures blocks are triggered by corroborated, multi-layered signals rather than isolated anomalies. The phased rollout approach—monitoring before enforcement—is critical for establishing accurate baselines.
How often should mobile threat detection rules be updated?
In a modern DevSecOps environment, rules should update continuously. Machine learning models governing sequential anomaly detection adapt dynamically to shifting traffic patterns. Structural security postures—such as updating compiler obfuscation logic to counter new reverse-engineering tools—should be automated to deploy with every application build pipeline. Threat intelligence feeds should trigger rule updates in near-real-time for known attack signatures.
What metrics indicate successful mobile threat detection?
Success is indicated by: a drastic reduction in Account Takeover incidents, elimination of API scraping bandwidth costs, lower false-positive rates in SOC alerts, consistent interception of requests from emulators and rooted devices before they impact backend databases, and measurable reduction in credential stuffing success rates. Track these metrics over time—the trend matters as much as the absolute numbers.