Here’s a fun fact that’ll keep you up at night: that mobile app your team just shipped? It’s probably already been reverse-engineered by someone with a $50 rooted Android phone and a weekend to kill — and that’s exactly why Red Team vs Blue Team mobile security has never mattered more.
The average mobile data breach now costs U.S. companies over $10 million according to IBM’s Cost of a Data Breach Report. Not “might cost” or “could cost”—does cost. And the scary part? Most of these breaches exploit vulnerabilities that could’ve been caught with a proper red team vs blue team mobile security program.
But here’s the thing: you can’t defend what you don’t understand. And you can’t understand your vulnerabilities until someone tries to exploit them. Red team vs blue team mobile security gives you exactly that—a systematic, adversarial approach to finding and fixing weaknesses before real attackers do.
That’s the power of red team vs blue team mobile security in 2025.
Think of it like this: if your mobile app is a fortress, the Red Team is the group of professional burglars you hire to break in. The Blue Team? They’re your security guards trying to catch them. And the whole point is to find your weaknesses before the actual bad guys do.
This isn’t your typical “run a vulnerability scanner and call it a day” security theater. We’re talking about sophisticated attack simulations that expose how real adversaries chain together mobile vulnerabilities, API exploits, and business logic flaws to exfiltrate your customer data.
In this guide, you’ll learn:
- what Red Team and Blue Team actually mean in mobile security,
- the most common attack scenarios Red Teams use against mobile apps and APIs,
- how Blue Teams detect and prevent these attacks,
- why controlled offensive testing saves you millions compared to post-breach cleanup,
- how to implement Red/Blue Team exercises that align with OWASP MASVS and compliance requirements.
Ready to see your mobile security through an attacker’s eyes?
Is your mobile app actually secure, or just “feels secure”?
Schedule a free security consultation with Iterators. We’ll show you what a Red Team sees when they look at your app—before the real attackers find it.
What Red Team vs Blue Team Mobile Security Actually Means
Let’s clear something up right away: red team vs blue team mobile security isn’t the same as general cybersecurity testing.
Sure, the concepts originated from military war games where offense and defense battle it out. But when we’re talking about red team vs blue team mobile security, we’re dealing with a completely different battlefield.
The Mobile Security Battlefield Is Different
In traditional network security, you’re defending a perimeter. Firewalls, intrusion detection systems, VPNs—you control the infrastructure and the access points.
In mobile security? The “client” is an untrusted device sitting in a potentially hostile user’s hands. They have physical access. They can root or jailbreak it. They can hook into your app’s runtime with tools like Frida. They can intercept every API call you make.
This is what makes red team vs blue team mobile security fundamentally different from any other form of security testing.
The key distinction between traditional web and mobile security comes down to control. In web security, you’re working with server-side code in a trusted execution environment behind a network perimeter you monitor. In mobile security, your code runs on untrusted devices where attackers have physical access, your API endpoints are exposed to the entire internet, and your business logic is split between client and server. That fundamental difference changes everything about how red team vs blue team mobile security operates.
Red Team: The Professional Burglars
The Red Team consists of offensive security professionals who simulate real-world attackers. But they’re not just running automated scanners and calling it a day. They’re thinking like actual adversaries: “How can I extract hardcoded API keys from this binary?” or “What happens if I replay this auth token 1,000 times?” or “Can I manipulate this payment flow to bypass authorization?”
Their job is to achieve specific mission goals—like exfiltrating customer PII or gaining unauthorized access to backend systems—while staying undetected as long as possible. The Red Team operates with what security folks call an “assume breach” mentality. They don’t ask if they can break in. They assume they already have and work backward from there.
Red team vs blue team mobile security requires specialized skills that go beyond general cybersecurity: reverse engineering APKs and IPAs, runtime instrumentation with Frida, mobile API abuse techniques, and deep knowledge of iOS and Android-specific security mechanisms.
Blue Team: The Always-On Defenders
The Blue Team is your defensive unit. They’re the security engineers, DevSecOps specialists, and incident responders responsible for monitoring threats around the clock, detecting anomalies in API traffic, responding to security incidents, hardening the infrastructure, and implementing runtime protections.
Unlike Red Team engagements (which are time-boxed campaigns), Blue Team operations are continuous. They’re managing SIEM platforms, configuring RASP solutions, tuning detection rules, and investigating alerts. Their success is measured by speed: how fast can they detect a threat (Mean Time to Detect) and how fast can they neutralize it (Mean Time to Response)?
Blue Teams defending mobile apps need specialized tools including Runtime Application Self-Protection (RASP), mobile app attestation, API request signing, and behavioral analytics specifically tuned for mobile traffic patterns.
| Feature | Red Team (Offense) | Blue Team (Defense) |
| Mindset | Adversarial, creative, unconventional | Systematic, protective, analytical |
| Operation Type | Periodic campaigns, time-boxed | Continuous 24/7 operations |
| Key Objectives | Expose flaws, bypass controls | Protect assets, detect intrusions |
| Primary Tools | Frida, Objection, Burp Suite, jadx | SIEM, XDR, RASP, EDR, IDS |
| Perspective | Attacker (External/Assume Breach) | Defender (Internal/Infrastructure) |
| Success Metrics | Objective achievement, stealth duration | Detection speed, response efficacy |
Why You Need Both Red Team vs Blue Team Mobile Security
Having just a Blue Team is like having security guards who’ve never seen an actual burglary. They know the theory, but they’ve never been tested under real attack conditions. And having just a Red Team? That’s like hiring burglars to rob your house and then doing nothing with the information.
The magic happens when they work together in a continuous improvement loop: the Red Team finds a vulnerability, the Blue Team detects (or fails to detect) the attack, both teams analyze what happened, the Blue Team implements better defenses, the Red Team tests those defenses, and the cycle repeats.This loop is what makes red team vs blue team mobile security so effective at hardening your mobile security posture.
Red Team vs Blue Team Mobile Security: Attack Scenarios Against Mobile Products

Let’s get into the fun stuff: how red team vs blue team mobile security exercises actually work when Red Teams attack mobile apps. Spoiler alert: it’s way more sophisticated than “run a vulnerability scanner and see what breaks.”
A. Reverse Engineering & Code Analysis
And in a proper red team vs blue team mobile security exercise, finding that treasure is the whole point. And the first step in any Red Team exercise is unpacking that map.
For Android apps, Red Teams use tools like apktool to unpack the APK and extract the DEX files (Dalvik Executable format), then run it through jadx to decompile the bytecode back into human-readable Java or Kotlin. What they’re looking for falls into two categories: hardcoded secrets and business logic vulnerabilities.
On the secrets side, Red Teams hunt for API keys for services like AWS, Firebase, and Stripe, along with OAuth client secrets, encryption keys, staging environment credentials, and internal API endpoints. Real talk? We’ve seen production apps with hardcoded database credentials in plaintext. Not obfuscated. Not encrypted. Just sitting there in a string constant.
On the business logic side, they look for premium feature checks that can be bypassed, payment validation done client-side instead of server-side, and admin functionality hidden behind simple boolean flags.
For iOS apps, the process is similar but uses different tools. Red Teams extract the IPA, locate the binary, and use tools like Hopper or Ghidra to disassemble the ARM code. iOS apps commonly leak secrets through hardcoded values in the binary, insecure Keychain usage, unencrypted local storage in Core Data or UserDefaults, and debug symbols left in production builds.
Red Teams also pay special attention to the AndroidManifest.xml file. Exported components—Activities, Services, Broadcast Receivers—that don’t require permissions can be triggered by other apps on the device. We’ve seen apps where you could trigger a “send receipt to email” function from a malicious app, allowing you to spam arbitrary emails through the legitimate app’s infrastructure.
B. API Abuse & Logic Bypass
Here’s where red team vs blue team mobile security gets really interesting. Most mobile apps are just pretty front-ends for backend APIs. And those APIs? They’re often hilariously vulnerable.
Man-in-the-Middle (MitM) Attacks work by setting up an intercepting proxy (Burp Suite or mitmproxy) and configuring the mobile device to route traffic through it. If the app doesn’t implement certificate pinning, the Red Team can see and modify every API request. What they typically find is alarming: user IDs in API paths that can be changed freely, authorization checks done client-side only, session tokens that never expire, and rate limiting that simply doesn’t exist.
Insecure Direct Object References (IDOR) represent the classic “change the user ID and access someone else’s data” vulnerability. The app makes a request to retrieve a user’s profile data. Change that user ID to someone else’s ID, and in a shocking number of apps, you get that user’s profile data with no additional authorization check. Red Teams automate this with scripts that iterate through thousands of user IDs and scrape the entire user database.
Business Logic Exploitation is where things get creative. These are the vulnerabilities that automated scanners never find because they require understanding how the app is supposed to work. We’ve seen loyalty programs where you can trigger reward logic by sending the same request multiple times, payment flows where you can manipulate the amount after authorization, referral systems where you can refer yourself infinitely, and promo codes that can be reused or combined when they shouldn’t be.
Race Conditions exploit timing windows in transaction processing by sending multiple simultaneous requests. The classic scenario: an app checks your account balance, then processes a withdrawal. By sending 10 withdrawal requests at the exact same moment, you can withdraw more than your balance before the system catches up.
C. Runtime Manipulation
This is where red team vs blue team mobile security gets truly terrifying. Welcome to the world of Frida.
Frida is a dynamic instrumentation toolkit that lets you inject JavaScript into running processes on mobile devices. It’s like having a debugger on steroids. With Frida, Red Teams can hook into any function and modify its behavior, read and modify variables in memory, bypass security checks in real-time, and intercept and modify method calls.
Bypassing SSL Pinning is one of Frida’s most common uses in Red Team exercises. SSL pinning is supposed to prevent MitM attacks by ensuring the app only trusts specific server certificates. Here’s how Red Teams bypass it in about 30 seconds: using a Frida script that hooks directly into the TrustManager’s certificate validation function and forces it to return success regardless of the certificate presented. Boom. Your “secure” pinning implementation is now useless.
Bypassing Root/Jailbreak Detection is equally straightforward. Apps often check if they’re running on a rooted or jailbroken device and refuse to run. Red Teams hook the detection functions and force them to return false—essentially telling your app “this device is totally not rooted, trust me”—regardless of the actual device state.
Manipulating Business Logic takes this even further. If your app has a premium feature check that returns whether a user has paid for premium access, Red Teams use Frida to hook directly into that function and force it to always return true—regardless of whether the user has actually paid. Congratulations, they just unlocked all your premium features without paying.
D. Data Exfiltration Chains
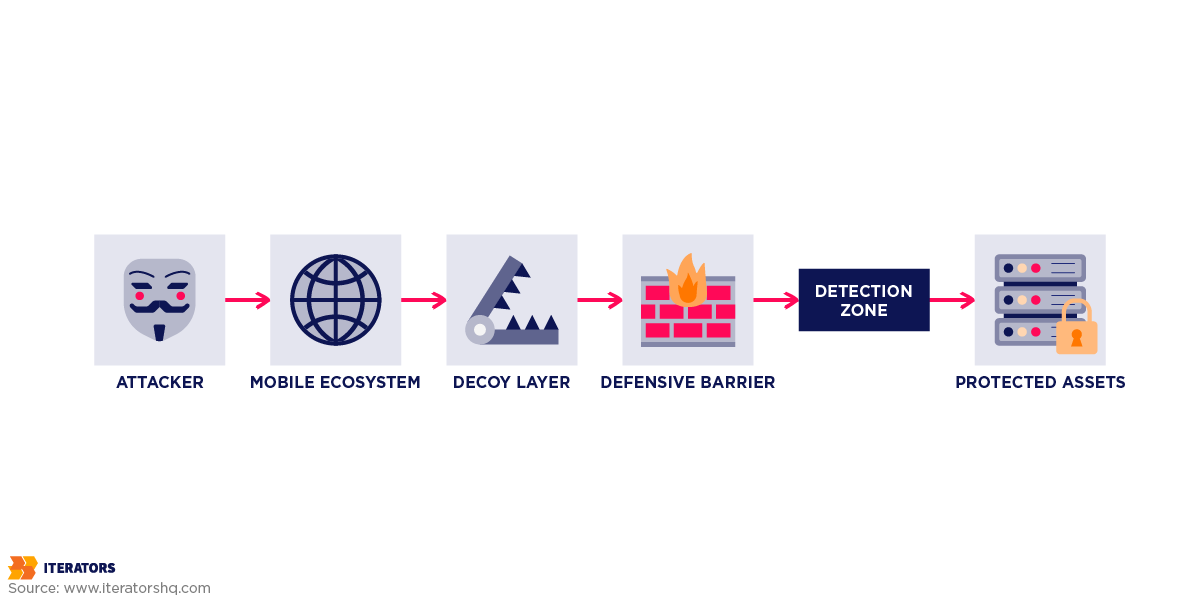
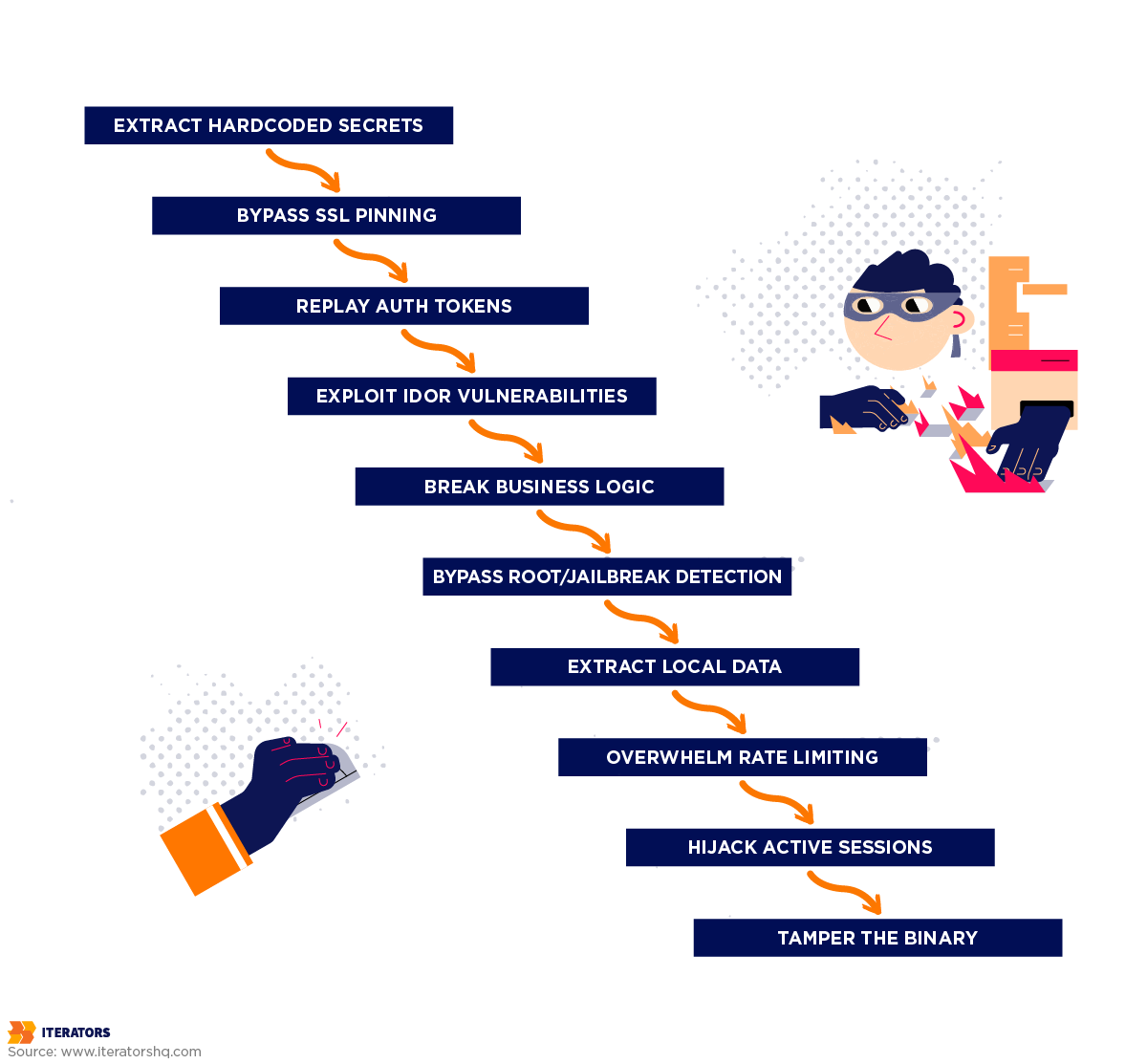
The most sophisticated red team vs blue team mobile security attacks don’t exploit a single vulnerability. They chain multiple weaknesses together to achieve their objective. A typical chain looks like this: extract an API endpoint from decompiled code through static analysis, intercept traffic through a MitM attack to understand the API request format, use Frida to disable certificate validation via SSL pinning bypass, modify user IDs in API requests through IDOR exploitation, automate a script to scrape the entire user database, and finally download PII for thousands of users.
Each individual step might seem minor. But together? They result in a catastrophic data breach. This is why red team vs blue team mobile security exercises are so valuable—they reveal how individual weaknesses combine into catastrophic breaches.
In one of our red team vs blue team mobile security engagements, we tested an e-commerce app where product prices were sent from client to server. You could buy a $500 item for $1 by modifying the price in the intercepted request. The Red Team demonstrated this, then automated it to “purchase” $50,000 worth of inventory for $100.
| Attack Technique | Tooling | Objective |
| Static Analysis | jadx, Apktool, Hopper | Extract hardcoded secrets and map app logic |
| Network Proxying | Burp Suite, mitmproxy | Intercept and manipulate API traffic |
| Runtime Hooking | Frida, Objection | Modify code execution and bypass client-side checks |
| Binary Tampering | Patching libraries (.so files) | Disable security features permanently in a modified binary |
| Data Scraping | Python scripts, automated proxies | Exfiltrate massive quantities of data via API abuse |
Red Team vs Blue Team Mobile Security: Blue Team Responsibilities

Okay, so in red team vs blue team mobile security, the Red Teams are basically professional hackers you hire to break your stuff. What’s the Blue Team doing while all this is happening? Ideally? Catching them. But in reality, Blue Team work is way more complex than just “stop the bad guys.” They’re building a multi-layered defense system that protects your mobile ecosystem across every attack surface.
A. Detection & Monitoring
The Blue Team’s first job in red team vs blue team mobile security is visibility. You can’t defend against what you can’t see.
Modern Blue Teams use machine learning to establish baselines of “normal” API behavior—typical request rates per user, common parameter values, expected geographic locations, and standard user agent patterns. Understanding how machine learning models detect anomalies is crucial for Blue Team effectiveness—read our breakdown of machine learning vs generative AI and their specific applications in security monitoring. When something deviates from that baseline—like a user making 1,000 requests per second or accessing the API from 50 different countries simultaneously—the system flags it immediately.
In red team vs blue team mobile security, Client Integrity Verification goes a step further by confirming that the app making API requests is actually your legitimate app, not a modified or repackaged version. This is accomplished through App Attestation (using Google Play Integrity API or Apple’s DeviceCheck to cryptographically verify the app’s identity), Request Signing (requiring API requests to include signatures that can only be generated by the legitimate app), and Environment Detection (checking for rooted or jailbroken devices, debuggers, or emulators).
Blue Teams also deploy Runtime Application Self-Protection (RASP) solutions that monitor the app’s execution environment for Frida or other instrumentation frameworks, debuggers attached to the process, memory tampering attempts, and suspicious function hooks. When RASP detects a threat, it can terminate the application, force a logout, clear sensitive session data, or send an alert to the security team.
B. Alerting & Response
Detection is useless if nobody acts on it. This is one of the most critical lessons from red team vs blue team mobile security exercises—detection without response is just expensive logging.
Blue Teams configure automated responses for common attack patterns. Rate limiting automatically throttles requests from suspicious sources. IP blocking temporarily isolates IPs exhibiting bot-like behavior. Session termination forces logout of compromised accounts. Captcha challenges require human verification for suspicious activity.
For situations that can’t be automated, Blue Teams establish clear escalation paths. Tier 1 handles common threats through automated responses. Tier 2 brings in a security analyst to investigate unusual patterns. Tier 3 escalates to a senior engineer for sophisticated attacks. Tier 4 calls in an external incident response team for major breaches.
When a Red Team (or real attacker) succeeds, forensic analysis becomes critical. Blue Teams review SIEM logs to trace the attack path, analyze network traffic captures, examine application logs for suspicious patterns, and conduct post-mortem analysis to prevent recurrence.
C. Defensive Architecture
The best lesson from red team vs blue team mobile security is not having vulnerabilities in the first place.
RASP is embedded directly into your application code, giving it the ability to protect itself. For a comprehensive technical breakdown of how RASP works in production environments, read our detailed guide on runtime protection mobile security and building defense-in-depth systems. It handles three core functions: environment detection (checking whether the app is running on a rooted device, in an emulator, or with a debugger attached), integrity verification (confirming the app binary hasn’t been tampered with and resources are original), and active response (terminating the app if threats are detected, disabling sensitive features, and sending telemetry to the security team).
API Gateway Security creates a protective layer between mobile clients and backend services. A well-configured gateway enforces OAuth 2.0 and JWT validation with scope-based access control, prevents abuse through rate limiting per user, IP, and API key, rejects malformed requests through schema validation, and captures all API traffic for analysis.
Backend hardening completes the red team vs blue team mobile security picture. This layered approach aligns with the NIST Cybersecurity Framework principles for building resilient information systems.The mobile app is just the front door—Blue Teams also secure the house. This means using parameterized queries and the principle of least privilege for database security, enforcing server-side validation of all critical operations (never trust client input), and managing secrets through services like AWS Secrets Manager or HashiCorp Vault rather than hardcoding them in code.
| Defensive Mechanism | Functionality | Strategic Value |
| Code Obfuscation | Renaming and restructuring code | Thwarts automated decompilers and casual analysis |
| RASP | Real-time runtime monitoring | Blocks dynamic instrumentation like Frida |
| App Attestation | Cryptographic identity verification | Prevents bot-driven API abuse and “fake client” access |
| API Gateway Security | Rate limiting, signing, validation | Protects against IDOR and parameter tampering |
| SIEM/XDR Monitoring | Log aggregation and ML analysis | Detects anomalies and exfiltration in real-time |
Using Red Team vs Blue Team Mobile Security to Validate Defenses
Here’s the brutal truth about red team vs blue team mobile security: you can implement every defensive control in the book, but you won’t know if they actually work until someone tries to bypass them. That’s the whole point of Red Team vs Blue Team exercises.
The Red Team vs Blue Team Mobile Security Validation Loop
Think of it like this:
Blue Team says: “We’ve implemented SSL pinning, so MitM attacks are impossible.”
Red Team says: “Hold my Frida script.”
30 seconds later…
Red Team: “Your pinning is bypassed. Here’s the intercepted traffic.”
This isn’t about embarrassing the Blue Team. It’s about exposing gaps before real attackers find them. That’s the entire philosophy behind red team vs blue team mobile security.
How Red Team Findings Inform Blue Team Improvements
When a Red Team succeeds in an attack, they document the exact attack path taken, the tools and techniques used, the defensive controls that failed, and the business impact if this were a real breach. The Blue Team uses this information to understand why existing controls didn’t prevent the attack, implement fixes through better detection rules and improved monitoring, validate those improvements by having the Red Team test again, and document lessons learned in updated security playbooks.
Real-World Example: The Token Replay Attack
In this red team vs blue team mobile security case study, a fintech app uses JWT tokens for authentication. During the Red Team exercise, the team intercepted a valid JWT token and discovered that tokens were valid for 24 hours, there was no rate limiting on API endpoints, and there was no device binding—tokens worked from any device. They captured a single valid token, replayed it 10,000 times from different IPs, scraped transaction history for thousands of users, and exfiltrated sensitive financial data.
The Blue Team responded by reducing token lifetime from 24 hours to 15 minutes, implementing refresh token rotation, adding device fingerprinting to bind tokens to specific devices, configuring rate limiting at 100 requests per minute per token, and setting up anomaly detection to flag unusual access patterns.
When the Red Team attempted the same attack again, the token expired after 15 minutes, rate limiting blocked mass requests, and anomaly detection flagged the suspicious behavior. Attack failed.
This is the red team vs blue team mobile security loop in action. Red Team finds vulnerability → Blue Team fixes it → Red Team validates fix → Everyone’s security posture improves.
Purple Teaming
Purple Teaming is an evolution of red team vs blue team mobile security where Red and Blue Teams collaborate in real-time rather than operating in silos. The Red Team announces they’re going to attempt a specific attack, the Blue Team monitors their detection systems, the Red Team executes, both teams review what was detected and what was missed, the Blue Team adjusts detection rules immediately, and the Red Team tests again. This accelerates the learning cycle dramatically.
Case Study: The API Parameter Tampering Fix
A food delivery app had an IDOR vulnerability where changing the user_id parameter in an order history API call returned other users’ orders. The Red Team’s automated script scraped 50,000 user records in 2 hours.
The Blue Team fixed it by implementing server-side authorization checks, removing user_id from query parameters (now derived from the authenticated session), adding logging for all order access attempts, and configuring SIEM alerts for rapid sequential order queries. The subsequent Red Team test returned 403 Forbidden errors and immediately triggered SIEM alerts. Attack blocked successfully.
Translating Red Team Findings into Defensive Improvements

Finding vulnerabilities is one thing. Fixing them without creating new problems is another. This is the practical challenge that every red team vs blue team mobile security program must solve.
Vulnerability Disclosure Without Exposing Implementation
There’s a tricky balance here: you need to communicate what was found and how to fix it, but you can’t publish a detailed blueprint for attackers.
A bad disclosure says: “Vulnerability: SSL pinning can be bypassed using Frida script. Fix: We use TrustManager.checkServerTrusted for validation.” This is bad because you just told attackers exactly which function to hook.
A good disclosure says: “Vulnerability: Runtime instrumentation can bypass certificate validation. Fix: Implemented multi-layered certificate validation with integrity checks. Detection: RASP now detects common instrumentation frameworks.” This describes the problem and solution without giving away implementation details.
Prioritization Frameworks
Not all vulnerabilities are created equal in red team vs blue team mobile security. Blue Teams prioritize fixes using a combined risk score that factors in severity (using CVSS scoring from Critical at 9.0-10.0 down to Low at 0.1-3.9), business impact (whether it exposes PII, causes financial loss, violates compliance, or damages brand reputation), and exploitability (skill level required, availability of public exploits).
The formula: Risk = (Severity × Business Impact × Exploitability) / Remediation Effort
This keeps Blue Teams focused on vulnerabilities that pose the greatest actual risk rather than just the easiest ones to fix.
Remediation Tracking
Blue Teams maintain a centralized vulnerability management system that tracks each finding through its lifecycle—from initial discovery with description and risk score, through assignment and remediation deadline, to final verified resolution. Key metrics include Mean Time to Remediate (MTTR), the percentage of critical vulnerabilities resolved within SLA, the size of the remediation backlog, and recurring vulnerability patterns that suggest systemic issues.
Continuous Improvement Programs
Red team vs blue team mobile security isn’t a project with an end date. It’s a continuous process built on quarterly Red Team exercises that rotate focus areas across the mobile app, APIs, backend, and infrastructure. Security Champions programs embed security-minded developers within each product team, creating feedback loops between development and security. Automated security testing in CI/CD pipelines handles Static Analysis Security Testing (SAST) on every commit, Dynamic Application Security Testing (DAST) in staging, dependency scanning, and container image scanning. Emerging technologies are creating new security paradigms that red team vs blue team mobile security programs must address—learn about AI in blockchain security and its implications for modern security architectures. Post-mortem reviews after every red team vs blue team mobile security exercise ask the hard questions: What worked? What didn’t? What should we focus on next?
Aligning with OWASP MASVS, Compliance & Standards
If you’re building mobile apps for any regulated industry—fintech, healthcare, e-commerce—you need to align your red team vs blue team mobile security exercises with established security standards.
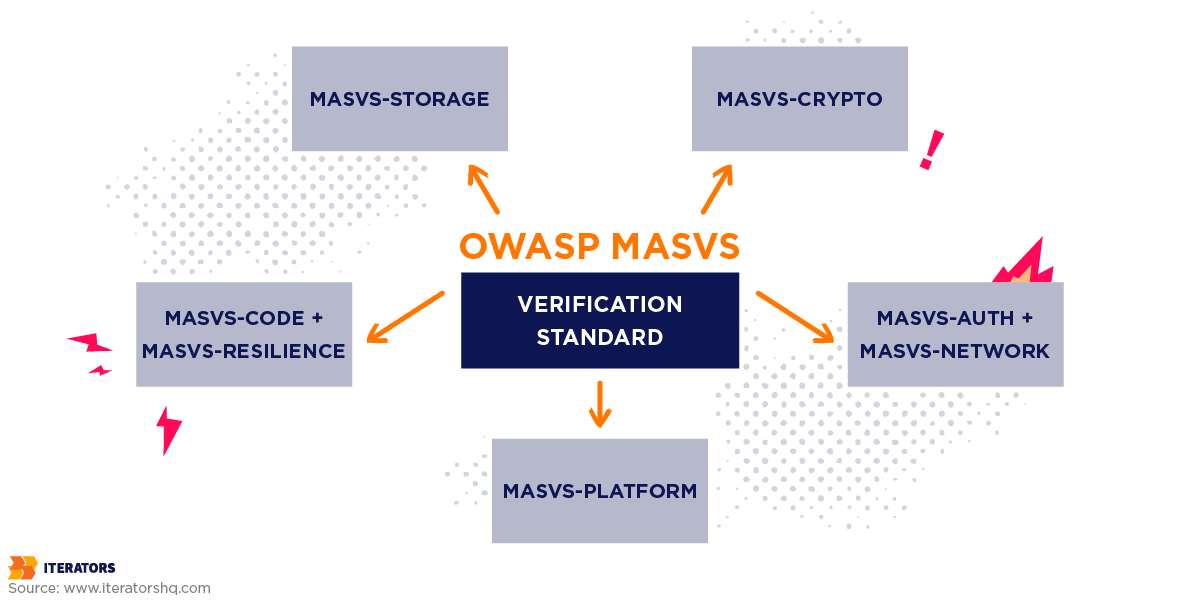
OWASP Mobile Application Security Verification Standard (MASVS)
When aligning your red team vs blue team mobile security program with compliance standards, The OWASP MASVS is the gold standard for mobile app security defining requirements across seven categories. MASVS-STORAGE covers secure data storage including encryption at rest, keeping sensitive data out of logs, and proper use of Keychain and Keystore. MASVS-CRYPTO addresses cryptography requirements including strong encryption algorithms (AES-256, RSA-2048+), secure random number generation, and proper key management. MASVS-AUTH covers authentication and session management including secure mechanisms, proper session handling, and account lockout policies. MASVS-NETWORK requires TLS 1.2+ for all connections, certificate pinning, and no sensitive data over unencrypted channels. MASVS-PLATFORM governs secure use of platform APIs and inter-process communication. MASVS-CODE enforces no hardcoded secrets, proper error handling, and secure coding practices. MASVS-RESILIENCE covers code obfuscation, anti-tampering protections, and runtime integrity checks.
Security Profiles (Verification Levels)
MASVS-L1 (Standard Security) is the baseline required for every production app—it covers fundamental security hygiene for any app handling user data. MASVS-L2 (Defense-in-Depth) is recommended for high-value apps in banking, healthcare, and fintech, adding certificate pinning, biometric authentication, and advanced session management. MASVS-R (Resilience Against Reverse Engineering) is a specialized profile for apps where IP protection is critical, focusing on anti-tampering and obfuscation for apps with valuable business logic or anti-fraud mechanisms.
Mapping Red Team vs Blue Team Mobile Security Exercises to MASVS
Your red team vs blue team mobile security exercises should explicitly test MASVS requirements. Attempting to extract hardcoded secrets from the binary tests MASVS-CODE-4, with Blue Team validation confirming secrets are stored in secure backends. Bypassing SSL pinning tests MASVS-NETWORK-1, with Blue Team validation confirming pinning can’t be bypassed without RASP detecting it. Using Frida to hook premium feature checks tests MASVS-RESILIENCE-2, with Blue Team validation confirming RASP detects instrumentation and terminates the app.
SOC2 Security Controls
Red team vs blue team mobile security exercises directly support several SOC 2 Trust Services Criteria. CC6.1 (Logical and Physical Access Controls) is tested when Red Teams attempt unauthorized API and backend access, with Blue Team controls covering authentication and authorization. CC6.6 (Vulnerability Management) is demonstrated through Red Team exploitation attempts and Blue Team patch management and remediation tracking. CC7.1 (Detection of Security Events) is validated when Red Teams attempt attacks while evading detection, with Blue Team SIEM and anomaly detection systems proving their effectiveness.
GDPR, CCPA, and Data Protection
GDPR Article 32 requires ‘appropriate technical and organizational measures’ to ensure data security. CCPA Section 1798.150 allows California consumers to sue if their data is breached due to lack of “reasonable security.” Red/Blue Team exercises satisfy both by demonstrating that you actively test your security controls, have processes to detect and respond to breaches, continuously improve your security posture, and proactively identify and fix vulnerabilities before they’re exploited.
Industry-Specific Compliance
PCI-DSS explicitly requires Red/Blue Team exercises through Requirement 6.6 (protect applications from known attacks) and Requirement 11.3 (implement penetration testing). HIPAA requires regular security evaluations under § 164.308(a)(8) and audit controls under § 164.312(b)—Red Team exercises provide the evaluation while Blue Team monitoring provides the audit logs.
Red Team vs Blue Team Mobile Security Cost-Effectiveness: Proactive Testing vs. Post-Breach Remediation

Let’s talk about money. Because at the end of the day, red team vs blue team mobile security is a business decision.
The Real Cost of a Mobile Data Breach
According to IBM’s 2025 Cost of a Data Breach Report, the average breach in the United States costs $10.22 million. This is exactly the kind of cost that a well-implemented red team vs blue team mobile security program is designed to prevent. Breaking that down: detection and escalation (forensic investigation, incident response, external consultants, crisis management) costs $1.47 million. Lost business from customer churn, reputation damage, and customer acquisition costs another $1.38 million. Post-breach response covering legal fees, regulatory fines, credit monitoring, and PR rehabilitation adds $1.20 million. Notification costs for customer communications and regulatory reporting add another $390,000.
And here’s the kicker: these costs assume you detect the breach quickly. If it takes months to discover you’ve been compromised, the costs escalate dramatically.
The Cost of Red/Blue Team Exercises
So what does offensive testing actually cost?
Professional Red Team Engagement:
- Small engagement: $40,000 – $60,000 (2-week mobile app penetration test)
- Comprehensive engagement: $80,000 – $150,000 (4-week full ecosystem test including mobile, APIs, backend)
- Continuous Red Team program: $200,000 – $400,000 annually (quarterly exercises, ongoing testing)
Building Internal Blue Team Capabilities:
- RASP solution: $50,000 – $150,000 annually (licensing for mobile RASP platform)
- SIEM/XDR platform: $100,000 – $300,000 annually (depending on log volume)
- Security personnel: $150,000 – $250,000 per security engineer (fully loaded cost)
Total annual investment for robust Red/Blue Team program: $500,000 – $1,000,000
Red Team vs Blue Team Mobile Security ROI Calculation
Let’s do the math:
Without Red/Blue Team Testing:
- Probability of breach: 20-30% annually (industry average)
- Average breach cost: $10.22 million
- Expected annual cost: $2.04 – $3.07 million
With Red/Blue Team Testing:
- Annual investment: $500,000 – $1,000,000
- Probability of breach: 5-10% (significantly reduced through proactive testing)
- Average breach cost: $10.22 million
- Expected annual cost: $510,000 – $1,022,000 (investment) + $511,000 – $1,022,000 (residual risk) = $1,021,000 – $2,044,000
Net savings: $1,019,000 – $1,026,000 annually
And that’s not even accounting for:
- Brand reputation preservation
- Customer trust maintenance
- Competitive advantage from demonstrable security
- Easier regulatory compliance
- Lower cyber insurance premiums
The Shadow AI Risk: $670,000
Red team vs blue team mobile security programs must now account for this emerging threat vector. This is when employees use unapproved AI tools (ChatGPT, Claude, etc.) to process company data without IT’s knowledge. Breaches involving Shadow AI add an average of $670,000 to the total cost.
Red Teams are now simulating AI-specific attacks including prompt injection to extract training data, data exfiltration through AI chat interfaces, bypassing AI content filters, and exploiting AI API endpoints. The intersection of AI and security creates new attack surfaces that require specialized knowledge—explore our analysis of generative AI in cybersecurity to understand how AI is both a threat and a defensive tool. Blue Teams need to inventory all AI tools in use, implement AI governance policies, monitor for data leakage through AI interfaces, and test AI systems with adversarial inputs.
| Cost Category | Average Cost | Trend |
| Detection and Escalation | $1.47 million | 10% decrease YOY |
| Lost Business and Revenue | $1.38 million | Sustained high impact |
| Post-Breach Response | $1.20 million | Includes fines and legal fees |
| Notification Costs | $390,000 | 10% decrease YOY |
| Shadow AI Breach Premium | +$670,000 | New category in 2025 |
Cost Savings from Security AI and Automation
Organizations that extensively use security AI and automation save an average of $1.9 million per breach compared to those with minimal automation. Building AI-powered security automation requires a strategic development approach—our guide on how to build an AI software solution walks through the technical and architectural considerations. Faster threat detection reduces Mean Time to Detect by 60%, automated response reduces manual effort, ML-powered anomaly detection catches threats humans miss, and false positive rates drop by 80%—allowing analysts to focus on real threats. This directly supports the business case for investing in a robust red team vs blue team mobile security program.
Implementing a Red Team vs Blue Team Mobile Security Program
Okay, you’re sold on red team vs blue team mobile security. Now how do you actually implement this?
When to Run Red Team vs Blue Team Mobile Security Exercises
Timing matters in red team vs blue team mobile security. Pre-launch testing is critical—run exercises before releasing a new mobile app, before major version updates, and before launching in new regulated markets. Quarterly testing provides a regular cadence for catching new vulnerabilities, testing recent code changes, and validating that previous fixes remain effective. Post-major releases warrant targeted testing after significant feature additions, infrastructure changes, or third-party integration updates. Event-driven testing should follow security incidents (yours or industry-wide), newly published attack techniques, or regulatory requirement changes.
Red Team vs Blue Team Mobile Security: Internal vs. External Teams
Internal Red Teams offer deep system knowledge, continuous availability, lower long-term cost, and the ability to participate in design reviews. Their weakness is familiarity—they can develop blind spots, face conflicts of interest, and lack the fresh perspective that comes from outside eyes.
External Red Teams bring fresh perspective, no organizational bias, specialized expertise, and credible third-party validation for compliance purposes. Their limitations include higher per-engagement cost, ramp-up time to understand your systems, and the fact that knowledge doesn’t stay in-house.
The best practice for red team vs blue team mobile security is using both: internal teams for continuous testing and quick iterations, external teams for quarterly comprehensive assessments and unbiased validation.
Tools & Techniques
The Red Team toolkit for static analysis includes jadx (Android DEX decompiler), apktool (APK unpacking), Hopper and Ghidra (iOS binary disassembly), and MobSF (automated mobile security framework). For dynamic analysis: Frida (runtime instrumentation), Objection (Frida-powered testing toolkit), Burp Suite Mobile Assistant, and mitmproxy. For API testing: Postman, ffuf (web fuzzer), and custom Python scripts for automation.
The Blue Team toolkit centers on RASP solutions (Guardsquare, Promon SHIELD, Zimperium zDefend), app attestation (Google Play Integrity API, Apple DeviceCheck), SIEM/XDR platforms (Splunk, Microsoft Sentinel, Datadog Security Monitoring), and API security gateways (Kong, Apigee, AWS API Gateway with WAF).
Red Team vs Blue Team Mobile Security Metrics & KPIs
Red team vs blue team mobile security effectiveness is measured by Objective Achievement Rate (percentage of mission goals achieved), Stealth Duration (how long Red Team remained undetected), Control Bypass Rate (percentage of security controls successfully bypassed), and Attack Path Diversity (number of different attack vectors discovered).
Blue Team effectiveness is measured by Mean Time to Detect (MTTD), Mean Time to Respond (MTTR), Detection Coverage (percentage of Red Team attacks detected), and False Positive Rate (percentage of alerts that weren’t actual threats).
Program maturity metrics include Vulnerability Remediation Rate, Recurring Vulnerability Rate, Control Effectiveness Improvement (reduction in successful attacks over time), and Security Debt Reduction (decrease in unresolved security issues). Business impact is tracked through Breach Avoidance (estimated costs prevented), Compliance Readiness (time saved in audit preparation), Insurance Premium Reduction, and Customer Trust Metrics like NPS scores and retention rates.
Red Team vs Blue Team Mobile Security: 10 Actionable Scenarios to Test
Want to get started with red team vs blue team mobile security? Here are 10 specific scenarios every mobile product should test:
- Hardcoded Secrets Extraction — Decompile the app binary, search for API keys, credentials, and encryption keys, and attempt to use discovered secrets.
- SSL Pinning Bypass — Set up an intercepting proxy, attempt to bypass certificate pinning, and intercept and modify API traffic.
- Token Replay Attack — Capture a valid authentication token, replay it from different devices and IPs, and test token expiration and rotation.
- IDOR (Insecure Direct Object Reference) — Identify user-specific API endpoints, modify user IDs or resource IDs, and attempt to access other users’ data.
- Business Logic Bypass — Map critical business flows around payment and premium features, attempt to manipulate client-side checks, and test for race conditions and timing attacks.
- Root/Jailbreak Detection Bypass — Run the app on a rooted or jailbroken device, use Frida to bypass detection, and verify the RASP response.
- Local Data Extraction — Access the app’s local storage (SQLite, SharedPreferences, Keychain), extract sensitive data, and verify encryption implementation.
- API Rate Limiting Test — Automate API requests at scale, attempt to exhaust rate limits, and test for account lockout mechanisms.
- Session Hijacking — Capture session tokens, test session binding to device and IP, and attempt session fixation attacks.
- Binary Tampering — Modify the app binary to disable security features, repackage and resign the app, and test app attestation detection.
Conclusion
Red team vs blue team mobile security isn’t a checkbox. It’s an ongoing battle between attackers who are constantly evolving their techniques and defenders who need to stay one step ahead.
The red team vs blue team mobile security approach gives you the only realistic way to validate your security posture: by simulating actual attacks in a controlled environment. Red Team attacks are offensive—reverse engineering your app, exploiting API vulnerabilities, chaining attacks together, and proving what’s actually exploitable rather than just theoretically vulnerable. Blue Team defense is continuous—detecting attacks in real-time, responding to threats, hardening infrastructure, and improving based on findings. The loop is what produces real security: Red Team finds vulnerabilities, Blue Team fixes them, Red Team validates the fixes, and the cycle repeats until your app is actually secure.
The economics are clear: spending $500,000-$1,000,000 annually on proactive red team vs blue team mobile security testing saves you $1-3 million in expected breach costs. But beyond the ROI, there’s something more important: trust. Your customers trust you with their data. Your investors trust you to protect the business. Your employees trust you to maintain a secure platform. Red team vs blue team mobile security exercises are how you earn and maintain that trust..
What’s Next?
This week, conduct a basic static analysis of your mobile app, review your API authentication mechanisms, and check for hardcoded secrets. This month, schedule your first Red Team engagement, implement basic RASP or app attestation, and set up API request logging and monitoring. This quarter, establish a quarterly Red/Blue Team testing cadence, build out your Blue Team capabilities with SIEM and XDR, and align your testing with OWASP MASVS requirements. On an ongoing basis, integrate security testing into your CI/CD pipeline, train developers on secure coding practices, and maintain a vulnerability remediation program.
The attackers aren’t waiting. They’re already probing your app, looking for weaknesses. The question is: will you find those weaknesses first?
FAQ
What’s the difference between Red Team testing and penetration testing?
Penetration testing is typically a point-in-time assessment focused on finding vulnerabilities. Red team vs blue team mobile security testing is more comprehensive—it simulates a real adversary attempting to achieve specific objectives (like exfiltrating customer data) using any means necessary, including social engineering, physical security, and chaining multiple vulnerabilities together. Red Team exercises also test the Blue Team’s detection and response capabilities, not just the existence of vulnerabilities.
How often should we run Red/Blue Team exercises?
For most organizations, quarterly Red Team exercises provide a good balance between thoroughness and cost. You should also run targeted exercises before major releases, after significant infrastructure changes, when new attack techniques are published, and after security incidents. For high-risk applications in banking or healthcare, monthly or continuous testing may be warranted.
Do we need to hire external Red Team experts or can we build an internal team?
The best approach is both. Build an internal team for continuous testing and quick iterations, but bring in external experts quarterly for fresh perspective, unbiased assessment, credible third-party validation for compliance, and specialized expertise in iOS-specific attacks or advanced API exploitation. External teams also provide valuable knowledge transfer to your internal security staff.
What tools do Red Teams use for mobile security testing?
The core Red Team mobile toolkit includes jadx and apktool for Android reverse engineering, Hopper or Ghidra for iOS binary analysis, Frida and Objection for runtime instrumentation, Burp Suite or mitmproxy for intercepting API traffic, MobSF for automated security analysis, and custom Python scripts for automation and data analysis. The specific tools vary based on the target platform and attack scenario.
How do we measure the success of Red/Blue Team programs?
Track Mean Time to Detect (MTTD), Mean Time to Respond (MTTR), Control Effectiveness (percentage of attacks successfully blocked), Vulnerability Remediation Rate, Recurring Vulnerability Rate, and Business Impact (estimated breach costs avoided). The goal isn’t to have zero successful Red Team attacks—it’s to improve these metrics over time.
Is Red/Blue Team testing required for compliance?
While not always explicitly required, Red/Blue Team testing strongly supports compliance. SOC 2 requires demonstrable security controls and vulnerability management. PCI-DSS explicitly requires penetration testing under Requirement 11.3. HIPAA requires regular security evaluations. GDPR requires “appropriate technical and organizational measures.” Red Team exercises provide evidence that you’re actively testing and improving your security posture, which auditors and regulators value highly.
Can small startups afford Red/Blue Team exercises?
Yes, but be strategic. Start with targeted testing on your highest-risk components—authentication, payment processing, PII handling. Use automated tools like MobSF and static analyzers for baseline testing. Hire external Red Teams for critical pre-launch assessments. Build security into your development process from day one (it’s far cheaper than fixing it later). A focused $40,000 Red Team engagement before launch can save you millions in breach costs later.
How do Red Team findings get prioritized for remediation?
Use a risk-based approach combining severity (CVSS score), exploitability (how easy is it to exploit?), business impact (what’s the potential damage?), and compliance requirements (does this violate regulations?). Calculate Risk = (Severity × Business Impact × Exploitability) / Remediation Effort. Focus on high-risk, high-impact vulnerabilities first. A critical authentication bypass takes priority over a low-impact information disclosure, even if the latter is easier to fix.
Ready to see what a Red Team would find in your mobile app?
At Iterators, we’ve been building and securing mobile applications for over 10 years. We know how attackers think because we’ve defended against them—and we know how to build apps that withstand real-world attacks.
Whether you need a comprehensive Red Team assessment, ongoing security consulting, or help building security into your mobile development process from day one, we’re here to help.
Schedule a free security consultation and let’s talk about protecting your mobile ecosystem before the real attackers find your vulnerabilities.
Because in mobile security, the best defense is knowing your weaknesses before anyone else does.