You’ve built an incredible SaaS product. Your tech stack is solid. Your UI is slick. Your customers love you. But without SOC2 compliance for SaaS, none of that matters when enterprise customers come knocking.
Then you get that email from a Fortune 500 prospect: “We’d love to move forward, but first—can you send us your SOC2 report?”
And just like that, your $500K deal hits a wall.
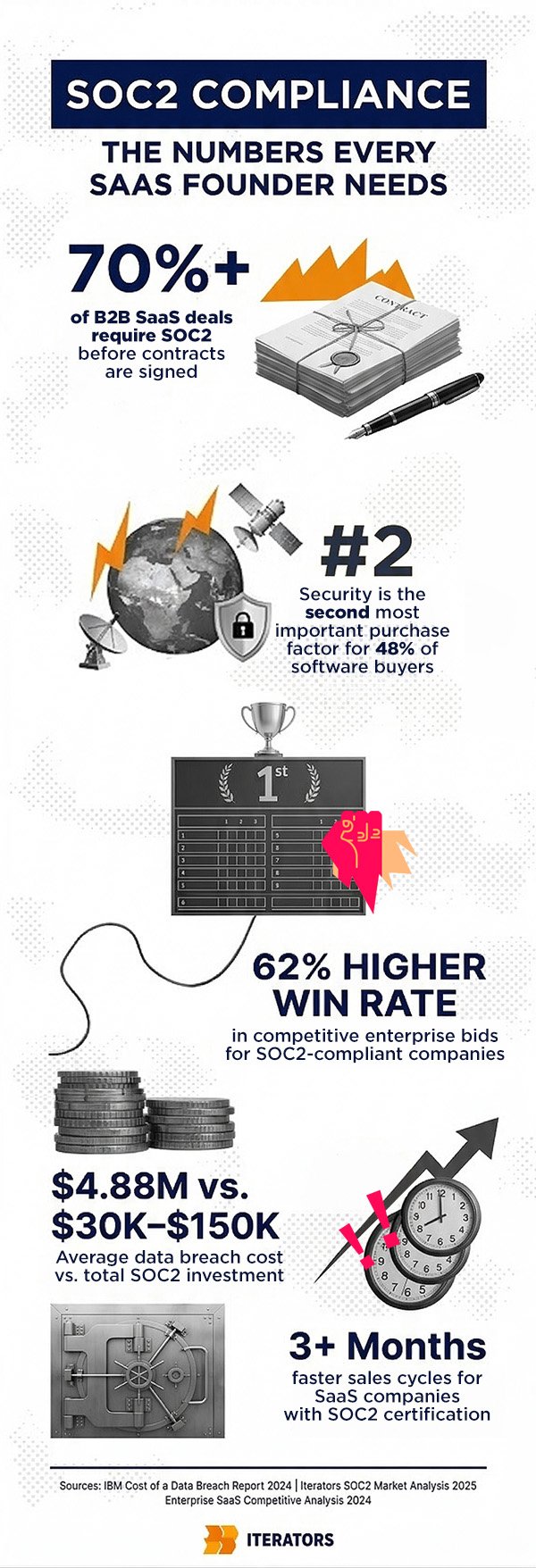
Here’s the brutal truth: in 2025, SOC2 compliance for SaaS companies isn’t a nice-to-have. It’s the price of admission to enterprise sales. Over 70% of B2B SaaS deals now require a SOC2 report before contracts get signed. Without it, you’re not even making it past the first procurement checkpoint.
This isn’t about checking boxes or making lawyers happy. SOC2 has become the universal language of trust in the cloud economy—the proof that you actually protect customer data the way you claim you do.
In this guide, we’ll break down everything you need to know about SOC2 compliance: what it is, why it matters, how much it costs, how long it takes, and most importantly—how to build it into your product from day one so you’re not scrambling when that enterprise deal shows up.
Building SOC2-ready infrastructure from the start? We can help. Book a free consultation with Iterators to discuss security-first architecture.
What Is SOC2 Compliance for SaaS? (And Why Every SaaS Company Is Talking About It)
SOC2 stands for System and Organization Controls 2—a framework created by the American Institute of CPAs (AICPA) to evaluate how service organizations handle customer data.
Think of it as a report card for your security practices. But instead of your teacher grading you, it’s an independent auditor who spends months examining your systems, policies, and controls.
The framework is built around five Trust Services Criteria:
- Security (mandatory for all reports)
- Availability
- Processing Integrity
- Confidentiality
- Privacy
Every SOC2 report must include Security. The other four are optional depending on what your customers care about and what kind of data you handle.
A Brief History: How SOC2 Got Here
SOC2 emerged in 2011 as cloud computing started eating the world. Before that, most enterprise software lived on-premise—behind corporate firewalls, managed by internal IT teams. Security was the customer’s problem.
But SaaS flipped that model. Suddenly, sensitive data was living in your infrastructure. Your servers. Your databases. Your responsibility.
Enterprises needed a standardized way to evaluate whether cloud vendors were actually trustworthy. The AICPA created SOC2 to fill that gap.
Fast forward to 2025, and SOC2 has become the de facto standard for B2B SaaS security. It’s not legally required (like HIPAA for healthcare or PCI DSS for payment processing), but practically speaking? It’s mandatory if you want to sell to enterprises.
The Business Case: Why SOC2 Compliance for SaaS Is No Longer Optional

Let’s talk about why this matters to your bottom line.
Enterprise Customers Won’t Buy Without SOC2
Here’s what happens when you don’t have SOC2:
- Sales team books a demo with a Fortune 500 prospect
- Demo goes great. Product fits perfectly
- Prospect sends over their security questionnaire
- You can’t answer half the questions with audited proof
- Deal stalls. Procurement says “come back when you’re compliant”
- Deal dies
This isn’t hypothetical. 48% of software buyers now consider security the second most important factor in their purchasing decisions—right after core functionality.
Without SOC2, you’re not competing on features. You’re disqualified before the conversation even starts.
Competitive Differentiation in Crowded Markets
In saturated SaaS categories, buyers are drowning in options. When five vendors all claim to have “enterprise-grade security,” how do they choose?
They scroll to the bottom of your website looking for the SOC2 badge.
Having SOC2 doesn’t just unlock deals—it creates trust arbitrage. You’re competing against startups that haven’t invested in compliance yet. Your certification is proof you’re serious. It signals maturity, stability, and long-term thinking.
Data backs this up: companies with robust data privacy measures see a 62% higher win rate in competitive enterprise bids.
How SOC2 Reduces Sales Cycle Friction
Enterprise sales cycles are notoriously long. Security reviews make them longer.
Without SOC2, every prospect sends you an 80-question security questionnaire. Your team scrambles to answer. Legal gets involved. Weeks turn into months.
With SOC2? You send a single PDF. The auditor already verified everything. Sales cycles can shrink by 3+ months.
At Iterators, we’ve seen this firsthand. One client was stuck in procurement hell with a major healthcare provider. After achieving SOC2 certification, they closed the deal in 90 days and unlocked $12 million in enterprise contracts.
“Achieving SOC2 certification was a pivotal move for our clients. Before, Our clients were buried in vendor assessments; now, we’re serious contenders for enterprise deals.”
— Jacek Głodek, Founder @ Iterators
How SOC2 Builds Trust with Investors and Partners
SOC2 isn’t just for customers. Investors care too.
VCs evaluating your Series A want to know you won’t become the next data breach headline. Strategic partners integrating with your API want proof you won’t leak their customers’ data. Advanced security architectures can further strengthen partner trust—explore our analysis of AI in blockchain security for additional data protection strategies.
SOC2 is risk mitigation for everyone in your ecosystem.
And here’s a stat that matters: the average cost of a data breach hit $4.88 million in 2024—a 10% increase from the previous year. Your SOC2 investment (typically $30K-$150K) is a rounding error compared to that exposure.
Understanding the SOC2 Framework: The Five Trust Services Criteria

SOC2 audits are structured around five Trust Services Criteria (TSC). Think of these as different lenses for evaluating your security posture.
Security (The Foundation)
Security is mandatory. Every SOC2 report must include it.
This criterion evaluates how you protect systems and data from unauthorized access, disclosure, and misuse. It covers the fundamentals:
- Firewalls and intrusion detection
- Multi-factor authentication (MFA)
- Role-based access control (RBAC)
- Encryption (at rest and in transit)
- Vulnerability management
- Incident response
In 2024, 100% of SOC2 reports included the Security criterion. It’s the baseline. Everything else builds on this.
Availability
Availability measures whether your system is operational and accessible as promised in your SLAs.
This matters for SaaS companies selling uptime guarantees. If you promise 99.99% availability, you need controls to back it up:
- Performance monitoring
- Disaster recovery (DR) plans
- Incident response playbooks
- Redundant infrastructure
- Automated failover
In 2024, 75.3% of SOC2 reports included Availability—up from 71% in 2023. Enterprises are demanding proof you won’t go down during their peak business hours.
Processing Integrity
Processing Integrity asks: does your system process data completely, accurately, and on time?
This is critical for fintech, e-commerce, and any platform handling transactions. Controls focus on:
- Data validation
- Error handling
- Quality assurance in your release pipeline
- Transaction reconciliation
Only 13.7% of SOC2 reports included this criterion in 2024. It’s niche—but if you’re processing payments or financial data, it’s non-negotiable.
Confidentiality
Confidentiality protects information designated as “confidential”—business plans, internal designs, intellectual property.
This criterion saw a massive surge in 2024, jumping from 34% to 64.4% of reports. Why? Enterprises are increasingly worried about competitive intelligence leaking through vendor relationships.
Controls include:
- Data classification policies
- Access restrictions
- Non-disclosure agreements
- Secure disposal procedures
Privacy
Privacy evaluates how you collect, use, retain, disclose, and dispose of personal information (PII).
This is the most complex criterion because it must align with regulations like CCPA, and state-level privacy laws.
It’s also the least common, appearing in only 6.8% of reports in 2024. Why so low? Because privacy compliance is hard. It requires legal expertise, cross-functional coordination, and ongoing policy updates.
But if you’re handling EU customer data or selling into healthcare, you can’t skip this.
Trust Services Criteria Summary
| Criterion | Mandatory? | 2024 Inclusion Rate | Key Focus |
|---|---|---|---|
| Security | Yes | 100% | Protection from unauthorized access |
| Availability | No | 75.3% | System uptime and accessibility |
| Processing Integrity | No | 13.7% | Accurate, complete processing |
| Confidentiality | No | 64.4% | Protection of confidential data |
| Privacy | No | 6.8% | PII handling and disposal |
Source: 2024 SOC2 benchmarking analysis
SOC2 Type 1 vs. Type 2: What’s the Difference?
SOC2 comes in two flavors: Type 1 and Type 2. Understanding the difference is critical for planning your certification roadmap.
SOC2 Type 1 Explained
Type 1 is a snapshot. It evaluates whether your controls are designed properly at a single point in time.
Think of it like a building inspection before construction finishes. The inspector checks the blueprints and confirms everything looks good on paper.
Timeline: 4-8 weeks
Cost: $5,000 – $25,000 (audit fees)
Best for: Startups needing to unblock deals quickly
Type 1 is faster and cheaper. It’s a great way to get your foot in the door with enterprise prospects who need something to satisfy procurement.
But here’s the catch: Type 1 doesn’t prove your controls actually work in production. It just proves you designed them correctly.
SOC2 Type 2 Explained
Type 2 is proof of effectiveness. It evaluates whether your controls operate consistently over a period of time (typically 3-12 months).
This is the gold standard. The auditor doesn’t just review your policies—they watch you execute them. They sample evidence across the entire observation period to confirm you’re doing what you say you’re doing.
Timeline: 6-12 months
Cost: $7,000 – $50,000+ (audit fees)
Best for: Companies selling into regulated industries or Fortune 500s
Type 2 is what enterprises really want. It’s the difference between “we have a security policy” and “we’ve been following this security policy for a year, and an auditor verified it.”
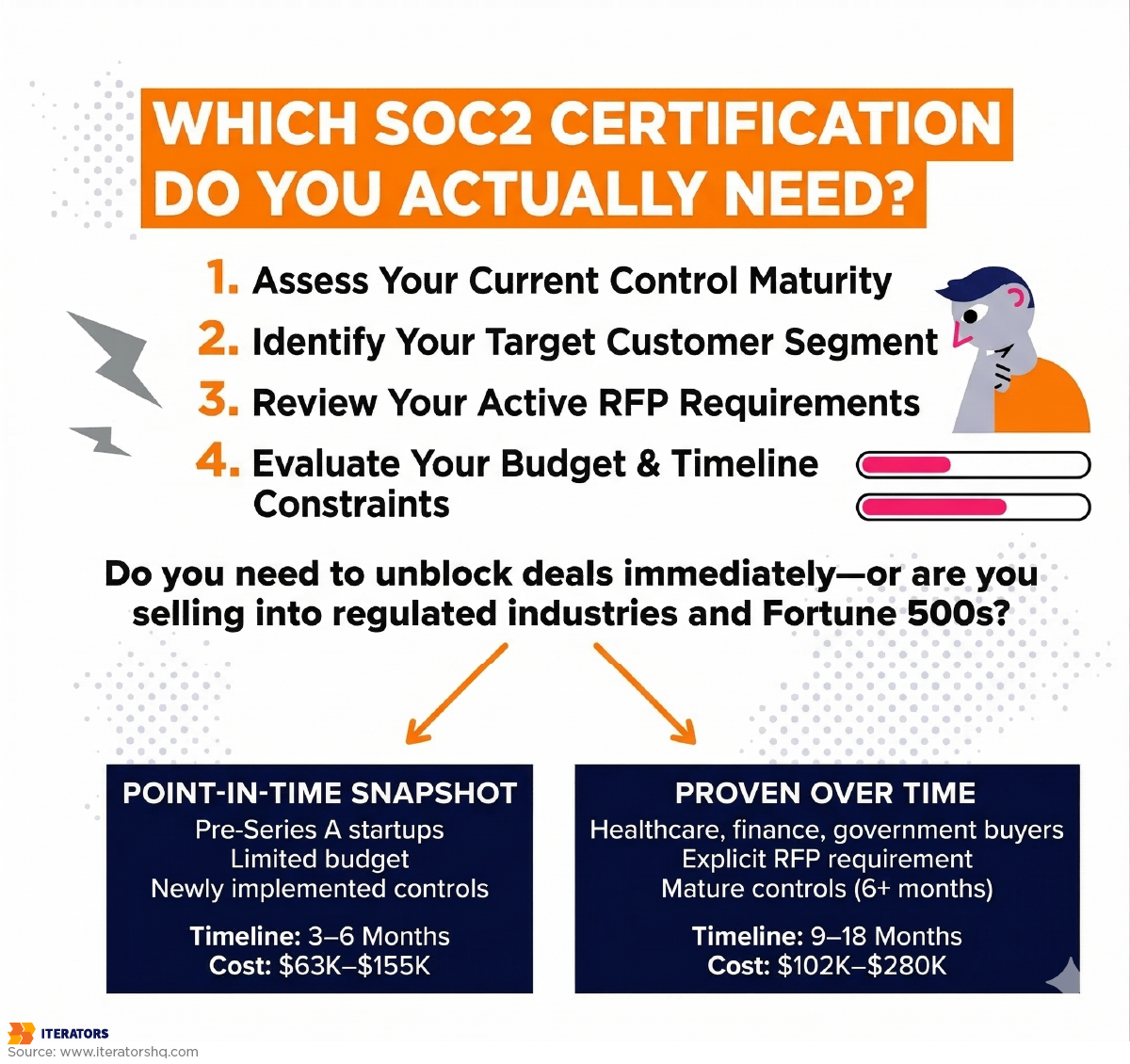
Which SOC2 Type Do You Need?
Start with Type 1 if:
- You need to unblock deals now
- You’re a pre-Series A startup with limited budget
- Your controls are newly implemented
Go straight to Type 2 if:
- You’re selling into healthcare, finance, or government
- Your customers explicitly require it in RFPs
- You’ve been operating with mature controls for 6+ months
Most companies follow this path:
- Achieve Type 1 to unlock initial enterprise deals
- Maintain controls for 6-12 months
- Upgrade to Type 2 for long-term credibility
SOC2 Type 1 vs. Type 2 Comparison
| Factor | Type 1 | Type 2 |
|---|---|---|
| Purpose | Design verification | Operational effectiveness |
| Audit Duration | 4-8 weeks | 6-12 months (observation period) |
| Cost | $5K – $25K | $7K – $50K+ |
| Best For | Quick deal unblocking | Long-term enterprise trust |
| Renewal | Annual | Annual (after initial observation) |
The SOC2 Audit Process: What to Expect

Getting SOC2 certified isn’t a single event—it’s a journey. Here’s what the process looks like from start to finish.
Step 1: SOC2 Readiness Assessment
Before you engage an auditor, you need to know where you stand.
A readiness assessment is an internal (or consultant-led) review of your current controls against SOC2 requirements. You’re looking for gaps:
- Do you have MFA enabled for all admin accounts?
- Are your databases encrypted?
- Do you have an incident response plan?
- Can you prove employees completed security training?
Timeline: 2-4 weeks
Cost: $5,000 – $15,000 (if using a consultant)
This step is critical. Jumping straight to an audit without readiness prep is like taking a final exam without studying. You’ll fail, waste money, and delay certification by months.
Step 2: Selecting an Auditor
Not all auditors are created equal.
You need a CPA firm that specializes in SOC2 audits and understands your industry. A firm that audits manufacturing companies won’t know the nuances of SaaS infrastructure.
What to look for:
- AICPA membership
- Experience with SaaS companies your size
- Reasonable pricing (get 3+ quotes)
- Good communication (you’ll be working together for months)
Timeline: 1-2 weeks
Cost: Varies (see pricing section below)
Step 3: Implementing SOC2 Controls
This is where the real work happens.
Based on your readiness assessment, you’ll need to implement missing controls and document existing ones. This includes:
- Writing security policies
- Configuring technical controls (MFA, encryption, logging)
- Training employees
- Setting up evidence collection processes
For Type 2, you’ll need to operate these controls for the entire observation period. That means if you implement MFA in January, your observation period can’t start until January.
Timeline: 2-6 months
Cost: $10,000 – $50,000 (internal labor + tools)
This is the most resource-intensive phase. You’re not just building controls—you’re changing how your company operates.
Step 4: The Audit Period
Once your controls are in place and operating, the formal audit begins.
The auditor will:
- Review your policies and procedures
- Test your technical controls
- Interview employees
- Sample evidence (logs, tickets, training records)
- Validate that controls operated consistently
For Type 1, this is a point-in-time review. For Type 2, they’re sampling across the entire observation period.
Timeline: 4-8 weeks (for the audit itself)
Cost: Included in audit fees
Expect a lot of back-and-forth. Auditors will ask for specific evidence, and you’ll need to produce it quickly. This is where having automated evidence collection (via GRC platforms) becomes a lifesaver.
Step 5: Receiving Your SOC2 Report
If everything checks out, you’ll receive your SOC2 report—a formal attestation that your controls meet the Trust Services Criteria.
This report is confidential. You don’t publish it publicly. Instead, you share it with prospects under NDA during the sales process.
Timeline: 1-2 weeks after audit completion
Validity: 12 months (then you need to renew)
Congratulations—you’re now SOC2 certified.
But here’s the thing: SOC2 isn’t a one-time event. You need to maintain your controls and renew annually. If your controls degrade, your next audit will fail.
Technical Requirements for SOC2 Compliance for SaaS

Let’s get into the weeds. What does SOC2 actually require from a technical standpoint?
The answer depends on your infrastructure, but here are the non-negotiables for modern SaaS companies.
Infrastructure & Cloud Security
Encryption Everywhere
- At rest: All databases, file storage, and backups must be encrypted (AES-256)
- In transit: All network traffic must use TLS 1.2 or higher
- Key management: Use managed key services (AWS KMS, Azure Key Vault) with documented rotation policies
Cloud Security Posture Management (CSPM)
You can’t manually track every S3 bucket and security group. You need automated scanning for misconfigurations:
- Public S3 buckets
- Overly permissive IAM roles
- Unencrypted databases
- Open security groups
Tools like AWS Security Hub, Azure Security Center, or third-party CSPM platforms are essential.
Infrastructure as Code (IaC) Security
If you’re using Terraform or CloudFormation, you need to scan your templates before deployment:
- Use tools like tfsec or checkov
- Integrate scanning into your CI/CD pipeline
- Block deployments that fail security checks
Access Control & Authentication
Multi-Factor Authentication (MFA)
This is non-negotiable. Every user—especially admins—must have MFA enabled.
Auditors will check:
- Is MFA enforced for all admin accounts?
- Can users bypass MFA?
- Are there exceptions? (There shouldn’t be)
Role-Based Access Control (RBAC)
Implement the Principle of Least Privilege. Users should only have access to what they need to do their job.
- Use RBAC across your entire stack (AWS IAM, Kubernetes namespaces, database roles)
- Document role definitions
- Review access quarterly and remove stale accounts
Single Sign-On (SSO)
For enterprise customers, SSO isn’t optional. It’s expected.
Integrate with identity providers like Okta, Azure AD, or Google Workspace. This gives you:
- Centralized access control
- Audit logs of who logged in when
- Easier offboarding (disable one account, revoke all access)
Logging, Monitoring & Incident Response
Centralized Logging
You need to capture logs from every layer of your stack:
- Application logs
- Database access logs
- Infrastructure logs (AWS CloudTrail, Kubernetes audit logs)
- Authentication logs
Ship everything to a centralized logging system (CloudWatch, Datadog, Splunk) with retention policies (typically 90 days minimum).
Real-Time Monitoring
Set up alerts for suspicious activity:
- Failed login attempts
- Privilege escalation
- Unexpected data access
- Infrastructure changes
For applications requiring advanced security monitoring, read our guide on runtime protection and mobile security that complements SOC2 compliance for SaaS requirements.
Incident Response Plan
Document how you’ll respond to security incidents:
- Who gets notified?
- How do you contain the breach?
- How do you communicate with customers?
- How do you conduct post-mortems?
Auditors will ask for evidence that this plan is tested—not just written and forgotten.
Data Encryption
At Rest
- Encrypt all databases (RDS encryption, disk encryption for VMs)
- Encrypt file storage (S3 server-side encryption)
- Encrypt backups
In Transit
- Force HTTPS for all web traffic
- Use TLS for internal service-to-service communication
- Disable legacy protocols (SSLv3, TLS 1.0, TLS 1.1)
Key Management
- Use hardware-backed key management (AWS KMS, Azure Key Vault)
- Rotate keys automatically
- Document key access policies
Vendor Risk Management
If you use third-party services (Stripe, Twilio, AWS), you need to evaluate their security too.
Auditors will ask:
- Do your vendors have SOC2 reports?
- Have you reviewed them?
- Do you have contracts with security SLAs?
Maintain a vendor inventory with security assessments for each.
Change Management & CI/CD Security
Code Review
- Require peer review for all code changes
- Use automated security scanning (SAST tools like SonarQube)
- Block merges that fail security checks
Deployment Controls
- Use blue/green or canary deployments
- Require approval for production changes
- Maintain rollback procedures
Container Security
If you’re using Kubernetes:
- Scan container images for vulnerabilities (Trivy, Clair)
- Enforce namespace isolation
- Use network policies to prevent lateral movement
SOC2 Technical Checklist
| Control Area | Example Requirements |
|---|---|
| Encryption | AES-256 at rest, TLS 1.2+ in transit, managed key rotation |
| Access Control | MFA for all users, RBAC, SSO integration |
| Logging | Centralized logs, 90-day retention, audit trails |
| Monitoring | Real-time alerts, incident response plan, tested runbooks |
| Vendor Management | Vendor inventory, SOC2 reviews, security SLAs |
| CI/CD Security | Code review, SAST scanning, deployment approvals |
| Container Security | Image scanning, namespace isolation, network policies |
How Long Does SOC2 Certification Take (And How Much Does It Cost)?
Let’s talk numbers.
Timeline Breakdown
SOC2 Type 1:
- Readiness assessment: 2-4 weeks
- Control implementation: 2-4 months
- Audit: 4-8 weeks
- Total: 3-6 months
SOC2 Type 2:
- Readiness assessment: 2-4 weeks
- Control implementation: 2-4 months
- Observation period: 6-12 months (operating controls)
- Audit: 4-8 weeks
- Total: 9-18 months
The biggest variable is your starting maturity. If you already have MFA, encryption, and logging in place, you can move faster. If you’re starting from scratch, expect the longer end of these ranges.
Cost Breakdown
SOC2 costs vary wildly based on company size, complexity, and how much you automate.
Here’s a realistic breakdown for a small to mid-sized SaaS company (50-250 employees):
| Cost Component | Type 1 | Type 2 |
|---|---|---|
| Audit Fees | $5K – $25K | $7K – $50K |
| Readiness Assessment | $5K – $15K | $10K – $25K |
| GRC Platform (Vanta, Drata) | $5K – $20K/year | $10K – $40K/year |
| Security Tool Upgrades | $5K – $25K | $10K – $50K |
| Legal & Policy Development | $3K – $10K | $5K – $15K |
| Internal Labor (400-600 hours) | $40K – $60K | $60K – $100K |
| Total | $63K – $155K | $102K – $280K |
Note: Internal labor is often the hidden cost. If you’re pulling senior engineers and CTOs away from feature development, the opportunity cost is real.
How to Reduce Costs
1. Use a GRC Platform
Tools like Vanta, Drata, and Secureframe automate evidence collection, reducing manual labor by 80-90%.
Example: Instead of screenshotting MFA settings every month, the platform pulls data automatically from your identity provider.
2. Start Early
Don’t wait until you need SOC2 to build controls. If you implement security best practices from day one, your “readiness gap” will be minimal.
3. Leverage Cloud Provider Compliance
AWS, Google Cloud, and Azure are already SOC2 compliant. You can inherit some of their controls (like physical data center security) instead of building your own.
4. Work with a Security-First Development Partner
At Iterators, we build SOC2-ready infrastructure from the start. Our clients don’t need to retrofit compliance—it’s baked into the architecture.
“Achieving SOC2 certification was a pivotal move for our clients. Before, we were buried in vendor assessments; now, we’re serious contenders for enterprise deals.”
— Jacek Głodek, Founder @ Iterators
SOC2 vs. Other Compliance Standards: What’s the Difference?

SOC2 isn’t the only compliance framework out there. Here’s how it compares to the other big ones.
SOC2 vs. ISO 27001
ISO 27001 is an international standard for information security management.
| Factor | SOC2 | ISO 27001 |
|---|---|---|
| Focus | Cloud service providers | Any organization |
| Geography | US-centric | Global |
| Audit | Third-party CPA | Accredited certification body |
| Cost | $30K – $150K | $50K – $200K |
| Timeline | 3-18 months | 6-24 months |
| Renewal | Annual | Every 3 years (with annual surveillance) |
When to choose SOC2: You’re a US-based SaaS company selling to US enterprises.
When to choose ISO 27001: You’re selling internationally (especially in Europe) or need a broader security framework.
Many companies pursue both—SOC2 for US customers, ISO 27001 for global credibility.
SOC2 vs. HIPAA
HIPAA (Health Insurance Portability and Accountability Act) is a US law that regulates how healthcare data is handled.
| Factor | SOC2 | HIPAA |
|---|---|---|
| Focus | Trust and security | Healthcare data protection |
| Legal Requirement | No (market-driven) | Yes (for covered entities) |
| Scope | All data types | Protected Health Information (PHI) only |
| Penalties | None (market loss) | Fines up to $1.5M per violation |
When to choose SOC2: You’re a general SaaS company.
When to choose HIPAA: You handle PHI (patient records, medical billing, etc.).
Important: If you’re a healthcare SaaS company, you likely need both. SOC2 proves general security; HIPAA proves PHI compliance.
Building SOC2 Compliance for SaaS Into Your Product From Day One

Here’s the uncomfortable truth: retrofitting compliance is expensive and painful.
Most startups build fast and loose in the early days. They ship features, ignore security, and figure they’ll “clean it up later.”
Then “later” arrives in the form of a $1M enterprise deal that requires SOC2. Suddenly you’re scrambling to implement controls, rewrite policies, and backfill documentation.
It’s chaos. It’s expensive. And it delays your deal by 6+ months.
Why Retrofitting SOC2 Compliance for SaaS Is a Nightmare
1. Technical Debt
Your codebase wasn’t built with security in mind. Now you need to:
- Add encryption to unencrypted databases
- Implement RBAC in a system with no roles
- Add audit logging to services that don’t log anything
This isn’t a weekend project. It’s months of engineering work.
2. Cultural Resistance
Your team is used to moving fast and breaking things. Suddenly you’re asking them to:
- Write security policies
- Complete compliance training
- Document every change
They’ll resist. They’ll complain. They’ll slow down.
3. Evidence Gaps
SOC2 Type 2 requires evidence over time. If you just implemented MFA last month, you can’t prove it’s been enforced for a year.
You’ll need to wait 6-12 months before you can even start a Type 2 audit.
Security-First Architecture
The alternative? Build compliance from the start.
This doesn’t mean over-engineering. It means making smart architectural choices early:
1. Choose the Right Cloud Provider
AWS, Google Cloud, and Azure are already SOC2 compliant. Their compliance becomes your foundation.
2. Use Managed Services
Don’t build your own auth system. Use Okta or Auth0.
Don’t manage your own databases. Use RDS or Cloud SQL with encryption enabled by default.
Managed services inherit the provider’s compliance, reducing your audit scope.
3. Implement Logging from Day One
Set up CloudTrail, VPC Flow Logs, and application logging before you need it. It’s easier to disable logging than to backfill it.
4. Enforce MFA and RBAC Early
Require MFA for all accounts. Define roles and permissions from the start.
It’s easier to maintain good habits than to fix bad ones.
5. Automate Everything
Use Infrastructure as Code (Terraform, CloudFormation) so your infrastructure is documented and repeatable.
Integrate security scanning into your CI/CD pipeline so every deployment is validated.
Working with a Development Partner Who Understands SOC2 Compliance for SaaS
At Iterators, our custom software development services have built SOC2-ready infrastructure for clients across healthcare, fintech, and enterprise SaaS.
We don’t treat compliance as an afterthought. It’s baked into our architecture from day one:
- Encrypted databases (at rest and in transit)
- RBAC and SSO integration for all user-facing apps
- Centralized logging with 90-day retention
- IaC scanning in CI/CD pipelines
- Automated vulnerability scanning for containers and dependencies
Our clients don’t scramble when enterprise deals show up. They’re already compliant.
Tools and Platforms to Automate SOC2 Compliance

Automation is the difference between SOC2 being a full-time job and a manageable process.
Here are the major players in the compliance automation space:
Vanta
Best for: Startups and growth-stage companies
Vanta is the speed leader. They focus on getting you compliant fast with minimal manual work.
Key features:
- 1,200+ automated checks per hour
- Integrations with 100+ tools (AWS, GitHub, Okta, etc.)
- Automated evidence collection
- Audit hub for seamless auditor collaboration
Pricing: Starts at ~$20K/year
Drata
Best for: Customization and multi-framework compliance
Drata positions itself as the “compliance automation platform” for companies that need more than just SOC2.
Key features:
- AI-driven automation
- Supports SOC2, ISO 27001, HIPAA
- Custom control frameworks
- Advanced reporting
Pricing: Starts at ~$25K/year
The intersection of AI and security compliance is evolving rapidly—explore how generative AI is transforming cybersecurity and SOC2 compliance for SaaS automation.
Secureframe
Best for: Mid-market companies with complex environments
Secureframe focuses on continuous compliance monitoring and risk management.
Key features:
- Real-time compliance posture dashboards
- Risk scoring
- Vendor risk management
- Automated policy generation
Pricing: Starts at ~$15K/year
Tugboat Logic
Best for: Enterprise-scale compliance programs
Tugboat Logic (now part of OneTrust) is designed for large organizations managing multiple frameworks across global teams.
Key features:
- Enterprise-grade workflow automation
- Multi-framework support
- Advanced analytics
- Custom integrations
Pricing: Custom (typically $50K+/year)
What These SOC2 Tools Can (And Can’t) Do
What they automate:
- Evidence collection (pulling logs, screenshots, configs)
- Policy templates
- Employee training tracking
- Vendor risk assessments
- Audit coordination
What they don’t do:
- Implement technical controls (you still need to configure MFA, encryption, etc.)
- Write your security policies (templates help, but you need to customize)
- Replace human judgment (automation flags issues, but you need to fix them)
Think of these platforms as force multipliers, not replacements for security expertise.
Common SOC2 Compliance for SaaS Mistakes (And How to Avoid Them)

Even with the best intentions, companies make predictable mistakes during their SOC2 journey.
1. Starting Too Late in the Sales Process
The mistake: You land a big enterprise prospect, they ask for SOC2, and you scramble to get certified in 30 days.
The reality: SOC2 takes 3-18 months. You can’t speed-run it.
How to avoid it: Start your SOC2 journey before you need it. If you’re targeting enterprise customers, certification should be on your roadmap 12 months out.
2. Underestimating the Time and Resources Required
The mistake: You assume SOC2 is a “side project” that your CTO can handle in their spare time.
The reality: SOC2 consumes 400-600 staff hours in the first year. That’s 10-15 weeks of full-time work.
How to avoid it: Budget for dedicated resources. Either hire a compliance lead or work with a partner who can own the process.
3. Treating It as a One-Time Project
The mistake: You get certified, celebrate, and forget about it.
The reality: SOC2 is continuous. You need to maintain controls year-round and renew annually.
How to avoid it: Build compliance into your operating rhythm. Quarterly access reviews, monthly vulnerability scans, annual policy updates.
4. Poor Documentation
The mistake: You implement controls but don’t document them. When the auditor asks for evidence, you scramble to recreate it.
The reality: Auditors need proof. No documentation = failed audit.
How to avoid it: Document as you go. Use GRC platforms to automate evidence collection. Treat documentation as part of the Definition of Done for every security initiative.
5. Ignoring Vendor Risk Management
The mistake: You focus on your own controls but ignore your vendors’ security.
The reality: If Stripe gets breached and leaks your customer data, you’re still liable.
How to avoid it: Maintain a vendor inventory. Review vendors’ SOC2 reports annually. Include security requirements in all vendor contracts.
Real-World Examples: SaaS Companies That Prioritized SOC2 Early
Let’s look at some real outcomes from companies that invested in SOC2.
Case Study: Healthcare SaaS Unlocks $12M in Revenue

The Problem:
A healthcare SaaS provider hit a revenue plateau. Large healthcare groups were pulling out of negotiations because the company lacked SOC2 certification.
The Solution:
They partnered with a development team (Iterators) to build SOC2-ready infrastructure. Instead of treating it as a compliance checkbox, they approached it as a cultural transformation.
The Results:
- Completed Type 2 audit in 6 months
- Closed $12M in enterprise deals within 3 months of certification
- Accelerated security reviews from 6 months to 3 weeks
- Improved customer retention by 20%
Case Study: Fintech API Scales with SOC2 Type 2
The Problem:
A fintech API provider had Type 1 certification but customers required “ongoing proof” of controls in production. Having worked extensively with fintech companies, we understand the unique SOC2 compliance for SaaS challenges financial services organizations face.
The Solution:
They automated evidence collection for change approvals and vulnerability SLAs, then pursued Type 2 certification.
The Results:
- Successfully passed Type 2 audit
- Reduced mean time to detect incidents by 40%
- Unlocked partnerships with 3 major banks
- Increased average deal size by 35%
Case Study: Enterprise Shared Services (KLIX)
The Problem:
A multinational consulting firm with 5,500 employees across 50 countries needed a time-tracking platform that met SOC2 standards.
The Solution:
Iterators developed KLIX, an enterprise-ready platform with SOC2 Trust Services Criteria embedded from the ground up.
The Results:
- Supported thousands of users across multiple time zones
- Enhanced global operational efficiency
- Provided custom reporting for business process excellence
- Maintained compliance across diverse regulatory environments
FAQ: Your Top SOC2 Compliance for SaaS Questions Answered
Do I need SOC2 if I’m just starting out?
Not immediately. If you’re pre-revenue or selling to small businesses, you can probably wait.
But if you’re targeting enterprise customers or raising a Series A, you should start planning for SOC2 within your first 12 months.
Can I get SOC2 certified in 3 months?
Type 1: Maybe, if your controls are already mature.
Type 2: No. Type 2 requires a 6-12 month observation period. There’s no way to speed that up.
What happens if I fail a SOC2 audit?
You don’t technically “fail”—but you can receive a qualified opinion, which means the auditor found issues with your controls.
This is almost as bad as not having a report at all. Most enterprises won’t accept qualified opinions.
If you receive a qualified opinion, you’ll need to fix the issues and re-audit.
Is SOC2 required by law?
No. SOC2 is a voluntary framework.
But practically speaking, it’s mandatory if you want to sell to enterprises. Many RFPs explicitly require SOC2 as a prerequisite for bidding.
How often do I need to renew SOC2?
Annually. Your SOC2 report is valid for 12 months.
After that, you need to undergo another audit to renew.
Can I use AWS’s SOC2 compliance to meet my own requirements?
Partially. AWS’s SOC2 report covers their infrastructure (data centers, physical security, etc.).
You can inherit those controls under the Shared Responsibility Model. But you’re still responsible for your application layer:
- How you configure AWS services
- How you manage access
- How you encrypt data
Think of it this way: AWS proves the building is secure. You still need to prove your apartment is secure.
Do I need SOC2 if I’m already HIPAA compliant?
Probably yes.
HIPAA proves you handle healthcare data correctly. SOC2 proves you have strong overall security.
Most healthcare enterprises want both.
How do I know which Trust Services Criteria to include?
Security is mandatory. For the others, ask your customers what they care about:
- Availability: If you promise uptime SLAs
- Processing Integrity: If you process transactions or financial data
- Confidentiality: If you handle sensitive business data
- Privacy: If you process PII or sell to EU customers
When in doubt, start with Security + Availability. You can add others later.
Conclusion: SOC2 Compliance as a Competitive Advantage
Here’s the bottom line: SOC2 compliance for SaaS companies is no longer a defensive play. It’s an offensive one.
Yes, you need it to unlock enterprise deals. Yes, it’s required to get past procurement. But the real value goes deeper.
SOC2 forces you to build better systems. It makes you think about security, resilience, and operational excellence from day one. It creates a culture of accountability and continuous improvement.
Companies that treat SOC2 as a checkbox exercise get minimal value. Companies that embrace it as a strategic advantage build trust, reduce risk, and accelerate growth.
The choice is yours:
Option 1: Wait until you need SOC2, then scramble to retrofit compliance into a system that wasn’t designed for it. Burn 6-12 months. Delay enterprise deals. Watch competitors win.
Option 2: Build SOC2-ready infrastructure from the start. Ship faster. Win bigger deals. Sleep better at night knowing your systems are actually secure.
At Iterators, we’ve been building security-first SaaS infrastructure for over 10 years. We’ve helped clients across healthcare, fintech, and enterprise software achieve SOC2 certification without sacrificing velocity.
We don’t just write code—we build trust.
Ready to build a SaaS product that’s enterprise-ready from day one? Schedule a free consultationto talk about security-first architecture and SOC2 compliance for SaaS.