You spent nine months building a relationship with a Fortune 500 procurement team. Your demos crushed it. The champion loves your product. Legal is circling the contract. Then the vendor security assessment lands in your inbox.
Three weeks later, the deal is dead.
Not because your product doesn’t work. Not because your pricing was wrong. Because your infrastructure couldn’t survive scrutiny from someone who actually knows what they’re looking at.
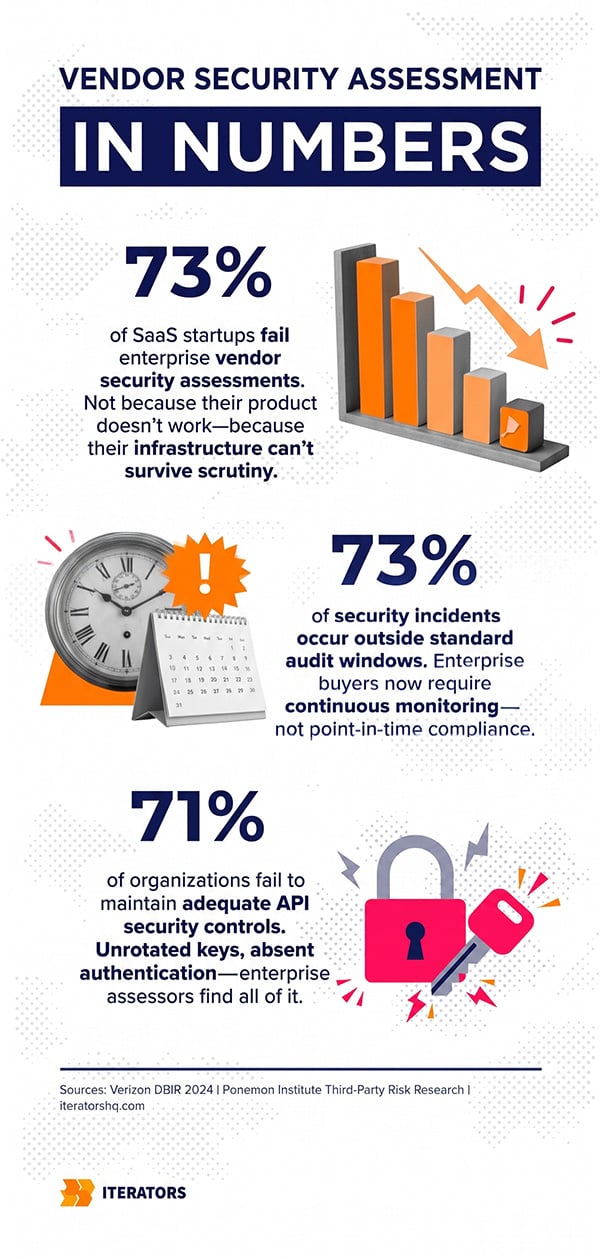
This is the story of most SaaS startups attempting to break into enterprise. And the frustrating part? The product was genuinely good. The security gaps that killed the deal were entirely fixable—just not in three weeks, not under pressure, and definitely not by filling out a questionnaire more carefully.
This guide exists to prevent that scenario. We’re going to show you exactly what Fortune 500 buyers check during a vendor security assessment, why most startups fail, and what it actually takes to build infrastructure that passes.
If you’re a founder or CTO somewhere between Series A and Series B, currently chasing enterprise logos or planning to, this is the most important thing you’ll read this year.
Free Consultation
Don’t Let Nine Months of Selling
Die in a Three-Week Assessment
Our engineers will audit your infrastructure against real Fortune 500 vendor assessment criteria — identifying the gaps that kill deals before a procurement team finds them first. We don’t produce reports. We fix what’s broken.
Assess My Security Gaps →The Hidden Cost of Failed Vendor Security Assessments

Why “Secure Enough for SMB” Isn’t Remotely Close to Enterprise Standards
There’s a dangerous assumption baked into the way most startups think about security. The logic goes: we haven’t been breached, our customers haven’t complained, we use AWS—we’re probably fine.
This works perfectly well for selling to other startups, small businesses, and mid-market companies with limited security oversight. These buyers don’t run formal vendor risk management programs. They check if you have a privacy policy and maybe ask whether you’re SOC 2 compliant. If you say “in progress,” they usually move on.
Enterprise buyers operate in a completely different universe during their vendor security assessment process.
A Fortune 500 CISO isn’t evaluating whether you’ve been breached. They’re evaluating the probability that you will be breached, and what happens to their data when you are. According to Ponemon Institute research on third-party risk, they’re thinking about the 12 vendor-caused security incidents their organization experiences annually on average. They’re thinking about the 195 days it typically takes to detect a SaaS-related breach. They’re thinking about the $4.88 million average cost of a data breach in 2024, which climbs to $9.4 million for US-based organizations.
The SMB buyer asks: “Does it work?”
The enterprise buyer conducting vendor security assessments asks: “What happens when it breaks, who finds out, how fast, and what’s our exposure?”
These are fundamentally different questions. And most startups aren’t built to answer the second set.
The Real Numbers: What a Failed Vendor Security Assessment Actually Costs Your Startup
The obvious cost is the lost deal. If you’re targeting enterprise, you’re probably talking about contracts worth $100K to $500K annually, sometimes much more. Lose three of those in a year to vendor security assessment failures, and you’re looking at a significant revenue gap that no amount of SMB sales will fill fast enough.
But the hidden costs are what really destroy companies.
Sales cycle waste. Enterprise sales cycles run six to eighteen months. Every hour your sales team, your legal team, and your executives invest in a deal that dies in vendor security assessment review is gone. That’s not just the direct cost—it’s the opportunity cost of every other deal those people could have been working.
Reputation damage. Enterprise procurement communities are small and tightly networked. Vendor security assessment failures get shared. If your product fails a vendor security assessment at one Fortune 500 company, there’s a non-trivial chance that information reaches other enterprise buyers in the same vertical.
Delayed market entry. The most painful cost is temporal. Retrofitting security onto an existing architecture to pass vendor security assessments takes six to twelve months minimum if you’re doing it properly. Every month you spend rebuilding infrastructure is a month your enterprise-ready competitors are closing the deals you can’t.
Compliance failure math is brutal. According to PWC’s vendor risk management research, maintaining a mature, continuous compliance program costs an organization approximately $5.47 million. The average financial damage of compliance failure is $14.82 million. That’s nearly a 3x multiplier on the cost of doing it wrong.
The business case for getting vendor security assessments right early isn’t even close.
The Competitive Disadvantage of Late-Stage Security Retrofitting
Here’s the thing nobody tells you at the beginning: security architecture is much easier to build correctly from the start than to retrofit later for vendor security assessments.
When you’re building your first version of a SaaS product, the decisions you make about data models, multi-tenancy, API design, and infrastructure shape everything that comes after. If you build a single-tenant architecture to ship fast, converting it to proper multi-tenant isolation with per-customer schema separation is a months-long engineering project that touches nearly every layer of your stack.
If you hard-code credentials into your codebase early on, cleaning that up requires finding every instance, rotating every key, implementing proper secrets management, and auditing your git history. If you’ve been doing it for two years across a team of fifteen developers, that’s a significant undertaking.
The competitors who built enterprise readiness in from day one aren’t just compliant—they’re faster. They’re closing deals you can’t even get through procurement. And while you’re spending engineering cycles on security retrofitting to pass vendor security assessments, they’re shipping features.
As Jacek Głodek, Founder of Iterators, puts it: “Relying on glossy pitch decks and vendor-provided security binders misses the real gaps: untested multi-tenant isolation, disaster-recovery blind spots, undocumented custom modules. True diligence surfaces these before you wire any funds.”
What Fortune 500 Buyers Actually Check in Vendor Security Assessments
The Five Pillars of Enterprise Vendor Security Assessment Requirements
Enterprise vendor security assessments aren’t random. They follow structured frameworks like the NIST Cybersecurity Framework designed to systematically evaluate every dimension of your security posture. Understanding the structure helps you understand where you’re likely to fail.
The five pillars that appear consistently across every major enterprise vendor security assessment framework are:
- Identity and Access Management — Who can access what, under what conditions, and how is that access controlled, monitored, and revoked?
- Data Protection and Cryptography — How is data protected at rest and in transit? How are cryptographic keys managed? What happens to customer data when the contract ends?
- Infrastructure Security and Resilience — What does your cloud architecture look like? How is it hardened? What are your disaster recovery capabilities?
- Monitoring, Detection, and Incident Response — How do you detect security incidents? How fast? What’s your response process? Can you prove it works?
- Compliance and Regulatory Alignment — Which frameworks do you comply with? Can you prove it with independent attestation, not just self-certification?
Each of these pillars contains dozens of specific controls that vendor security assessments probe systematically.
The Vendor Security Assessment Questionnaire Frameworks: What’s Actually Landing in Your Inbox
When a Fortune 500 procurement team sends you a vendor security assessment questionnaire, it’s usually built on one of a handful of established frameworks.
The Standardized Information Gathering (SIG) questionnaire, maintained by the Shared Assessments Program, is the most common vendor security assessment tool. It comes in two flavors: SIG Lite for lower-risk vendors (two to three days to complete for a prepared team) and SIG Core for critical infrastructure vendors (five to seven days, and that’s if you actually have the answers).
The Cloud Security Alliance CAIQ focuses specifically on cloud computing controls and maps to the Cloud Controls Matrix. If you’re cloud-native, expect this vendor security assessment framework.
The Vendor Security Alliance (VSA) tools focus heavily on privacy law compliance—GDPR, CCPA, and similar regulations. If you’re selling to European enterprise buyers or companies with significant EU exposure, this vendor security assessment becomes critical.
Government and federal agency contracts bring in NIST SP 800-171 and FedRAMP requirements, which are substantially more demanding than commercial enterprise vendor security assessment standards.
Here’s the brutal reality about these vendor security assessment questionnaires: they’re not designed to be fooled. Enterprise security teams have seen every version of “we have a policy for that” and “this is on our roadmap.” They know what a real answer looks like versus a marketing answer. When you claim you have encrypted backups with audit trails and they ask for the documentation, you either have it or you don’t.
Infrastructure Security Controls That Make or Break Vendor Security Assessments
When enterprise buyers dig into your infrastructure during vendor security assessments, they’re looking for specific architectural evidence, not policy documents.
Multi-tenancy isolation is often the first thing that kills deals for SaaS startups in vendor security assessments. Enterprise buyers want proof that their data cannot leak into another customer’s environment. This requires sharded architecture with per-customer schema separation managed at the application layer, not just logical separation within a shared database. The difference between “we use row-level security” and “we have per-customer schema isolation with cryptographic separation” is the difference between a failed assessment and a passed one.
Infrastructure as Code is another area where startups frequently fall short in vendor security assessments. Enterprise buyers want evidence that your infrastructure configurations are version-controlled, reproducible, and subject to change management. If your team is manually configuring servers, applying patches through SSH, and managing environments through undocumented tribal knowledge, that’s a red flag. Terraform-managed infrastructure with documented runbooks and automated deployment pipelines is the baseline expectation.
Secrets management is where many startups get caught with their hands in the cookie jar during vendor security assessments. Hard-coded API keys in repositories, credentials stored in environment variables without rotation policies, database passwords that haven’t changed since the company was founded—enterprise security teams find all of this. The standard is Vault-backed secrets management with automated rotation and audit logging.
Penetration testing requirements are non-negotiable for most enterprise vendor security assessments. They want evidence of regular, independent third-party penetration testing with documented remediation of findings. Not an automated vulnerability scan—actual adversarial testing by qualified external parties. And they want to see how fast you remediate critical findings.
Data Protection and Privacy Requirements in Vendor Security Assessments
The data protection pillar of vendor security assessments has become significantly more complex over the past five years, driven by the proliferation of privacy regulations across jurisdictions.
Encryption standards are table stakes in vendor security assessments. Data encrypted at rest and in transit using current, uncompromised algorithms is the absolute minimum. But enterprise buyers increasingly ask about key management practices. Are your encryption keys stored separately from the encrypted data? Are they managed through a dedicated key management service? What’s your key rotation policy?
Data residency and sovereignty requirements have become deal-breakers for many enterprise vendor security assessments, particularly those with European operations or customers. GDPR requirements around data processing agreements, data subject rights, and cross-border transfer mechanisms must be built into your architecture, not bolted on as an afterthought.
Data lifecycle management is often where startups reveal how immature their data practices actually are during vendor security assessments. Enterprise buyers want documented procedures for data retention, data destruction upon contract termination, and data portability. If you can’t demonstrate a tested process for completely and provably deleting a customer’s data when they offboard, that’s a significant problem.
HIPAA, PCI DSS, and industry-specific requirements layer on top of baseline GDPR and CCPA compliance for buyers in regulated industries conducting vendor security assessments. Healthcare and financial services buyers add substantial additional requirements that require specific architectural accommodations.
Access Management and Identity Controls Under Vendor Security Assessment Scrutiny
The 2024 Verizon Data Breach Investigations Report fundamentally reframed how enterprise buyers think about vendor risk during vendor security assessments. Modern attacks don’t break through hardened perimeters—they log in using compromised identities and stolen credentials. This has made identity and access management the most scrutinized dimension of vendor security assessments.
Multi-Factor Authentication is no longer optional in vendor security assessments. Enterprise buyers want MFA enforced across all user accounts, all administrative accounts, and all developer access to production systems. “We encourage MFA” is not an acceptable answer. “MFA is enforced and cannot be bypassed” is the answer they’re looking for.
Single Sign-On integration is a requirement for enterprise deployment, not a nice-to-have feature. Your product must support SAML 2.0 or OpenID Connect integration with enterprise identity providers like Okta, Azure Active Directory, or OneLogin. If you can’t integrate with their identity infrastructure, you can’t be deployed at scale.
Privileged access management requirements probe how your organization handles administrative access to production systems. Who has access to production databases? How is that access granted, monitored, and revoked? What happens when an employee leaves? Enterprise buyers want to see least-privilege principles enforced with documented access review processes.
API security is an area where 71% of organizations fail to maintain adequate controls during vendor security assessments. Enterprise buyers examine how you manage API keys, OAuth tokens, and service account credentials across your application ecosystem. Unrotated API keys, overly permissive service accounts, and absent API authentication are common findings that terminate assessments.
Monitoring, Logging, and Incident Response Capabilities in Vendor Security Assessments
Enterprise buyers conducting vendor security assessments have learned, often through painful experience, that the question isn’t whether a security incident will occur—it’s whether you’ll know about it when it does.
The requirement for continuous monitoring rather than point-in-time auditing has become a defining characteristic of modern vendor security assessments. Consider that 73% of security incidents occur outside standard audit windows. A clean annual audit means very little if you have no visibility into what’s happening between audits.
Enterprise buyers want to see structured application logging with centralized aggregation, retention policies that meet regulatory requirements, and active monitoring with alerting. They want to know that if someone accesses a customer record they shouldn’t have access to, someone on your team will know about it within hours, not months.
Incident response plans must be documented, tested, and recent. “We have a plan” isn’t sufficient for vendor security assessments. Enterprise buyers want to see the plan, understand who’s responsible for what, and see evidence that it’s been tested through tabletop exercises or actual incident simulations. They want to know your Recovery Time Objective and Recovery Point Objective, and they want evidence that your disaster recovery capabilities have been validated.
Business continuity planning requirements extend beyond technical recovery. Enterprise buyers want to understand how your organization maintains operations during a security incident, what your communication protocols are for notifying affected customers, and how you manage the regulatory notification requirements that apply to data breaches.
The Seven Most Common Security Gaps That Kill Vendor Security Assessments

Gap #1: Missing or Inadequate Documentation
The most common reason startups fail vendor security assessments isn’t that their security is terrible—it’s that they can’t prove their security is adequate.
Enterprise auditors conducting vendor security assessments need documentation. Policies, procedures, architectural diagrams, runbooks, incident response plans, disaster recovery procedures, access control matrices. If your security practices exist only in the heads of your engineering team and nowhere else, you will fail every vendor security assessment that asks you to demonstrate them.
The documentation gap is particularly acute for startups that have grown rapidly. Things that worked fine when there were five engineers become dangerous when there are fifty. The informal security practices that everyone “just knows” become the undocumented vulnerabilities that enterprise assessors find.
Gap #2: Unencrypted Data at Rest and in Transit
This sounds basic because it is basic. And yet it remains one of the most common findings in enterprise vendor security assessments of early-stage SaaS companies.
The typical failure pattern: encryption is enabled for the primary production database, but not for backup storage, log aggregation systems, development and staging environments, or data exports. Enterprise buyers check all of these. Finding one unencrypted data store is enough to fail the vendor security assessment.
Gap #3: Weak Access Controls and Authentication
The access control gap is almost universal in startups that haven’t been through a formal vendor security assessment. The common failures include: shared administrative credentials used by multiple team members, no formal offboarding process that includes credential revocation, production access granted to developers who no longer need it, and administrative interfaces accessible from the public internet without additional authentication.
Gap #4: No Security Monitoring or Incident Response Plan
When an enterprise buyer conducting a vendor security assessment asks “how would you know if you were breached right now?” and the honest answer is “we’d probably find out when a customer complained,” that deal is over.
The absence of real-time security monitoring isn’t just a compliance gap—it’s evidence of a security culture problem. Enterprise buyers interpret it as a signal that security isn’t a priority, which means every other control they’ve seen is probably also inadequate.
Gap #5: Inadequate Vendor and Third-Party Risk Management
Here’s an irony that enterprise buyers fully appreciate: the startup being assessed for vendor risk often has no vendor risk management program of its own.
If you’re using dozens of third-party services, APIs, and software dependencies without any formal process for evaluating their security posture, you’re introducing your customer’s data to an uncontrolled chain of risk. Enterprise buyers want to see that you manage your own vendor risk with the same rigor they’re applying to you in their vendor security assessment.
Gap #6: Missing Disaster Recovery and Business Continuity Plans
Documented RTO and RPO commitments without tested disaster recovery capabilities are worse than having no commitments at all during vendor security assessments. Enterprise buyers have seen too many startups claim 4-hour RTO on their questionnaires and then fail to recover a test environment in under 48 hours.
The gap here is almost always between what’s documented and what’s been validated. Enterprise buyers increasingly require evidence of recent disaster recovery testing, not just the existence of a plan.
Gap #7: Insufficient Security Training and Awareness Programs
Security isn’t just an infrastructure problem—it’s a human problem. Phishing attacks, social engineering, and credential theft succeed because people make mistakes. Enterprise buyers conducting vendor security assessments want evidence that your team receives regular security awareness training and that you have processes for identifying and responding to human-vector attacks.
The Enterprise Readiness Preparation Framework for Vendor Security Assessments
The Honest Truth About Vendor Security Assessment Timelines
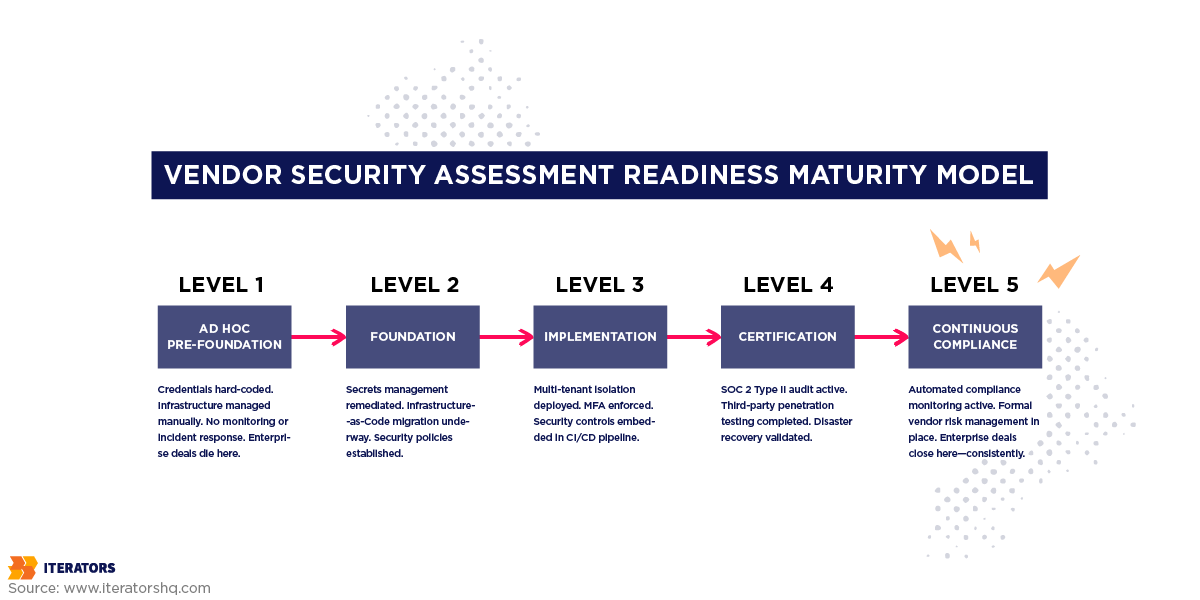
Before we get into the framework, let’s establish something important: you cannot pass a rigorous enterprise vendor security assessment in thirty days if your infrastructure isn’t already enterprise-ready. Anyone telling you otherwise is selling you something.
Real enterprise readiness takes six to twelve months of focused engineering work, and that’s assuming you start from a reasonably mature foundation. If you’re starting from a typical early-stage startup architecture, plan for twelve to eighteen months.
This is why the most important strategic insight in this entire article is: start before you need it. The startups that win enterprise deals consistently are the ones who decided to build for vendor security assessment readiness before they had enterprise customers to justify the investment.
Phase 1: Foundation (Months 1-3)
The foundation phase is about getting honest about where you actually are, fixing the things that are definitively broken, and establishing the infrastructure required for everything that follows.
Infrastructure audit. Before you can fix anything, you need to know what’s broken. This means a comprehensive review of your cloud architecture, access controls, data flows, third-party dependencies, and existing documentation. Be brutally honest. The goal isn’t to create a report that looks good—it’s to find everything that would fail a vendor security assessment.
Secrets management remediation. If you have hard-coded credentials anywhere in your codebase or infrastructure, this is the highest-priority fix. Implement Vault-backed secrets management, rotate all existing credentials, and establish policies that prevent credential exposure going forward. This is foundational—everything else depends on it.
Infrastructure as Code migration. If your infrastructure isn’t fully defined in version-controlled Terraform or equivalent, begin that migration. This isn’t just about compliance—it eliminates the configuration drift that causes unpredictable security failures and makes your infrastructure auditable.
Documentation baseline. Begin documenting everything. Security policies, access control procedures, incident response plans, architectural diagrams. Even if the policies describe processes that need improvement, having them documented is the prerequisite for everything else.
Phase 2: Implementation (Months 4-6)
The implementation phase is where you build the controls that your documentation describes and that vendor security assessments will validate.
Multi-tenant isolation. If your architecture doesn’t provide proper data isolation between customers, this is where you address it. The scope and complexity of this work depends heavily on your existing architecture—for some startups, it’s a significant refactoring effort.
Monitoring and logging infrastructure. Deploy centralized log aggregation, implement structured logging across your application, set up alerting for security-relevant events, and establish the observability foundation required for continuous monitoring. This is the infrastructure that will make your incident response plan actually executable during vendor security assessments.
Access control hardening. Implement least-privilege access across all systems, establish formal access review processes, deploy MFA enforcement across all accounts, and document your privileged access management procedures.
CI/CD security integration. Embed security controls directly into your deployment pipeline—container image scanning, dependency vulnerability scanning, static analysis, and automated compliance checks. Security in the pipeline means security issues are caught before they reach production.
Phase 3: Certification (Months 7-9)
The certification phase is where you get independent validation of the controls you’ve built—the evidence that passes vendor security assessments.
SOC 2 Type II audit. The SOC 2 Type II audit validates that your controls have operated effectively over an extended period—typically six to twelve months. This is why you can’t shortcut the earlier phases. You need the controls to be running before the audit period begins.
Penetration testing. Commission an independent third-party penetration test of your application and infrastructure. Use the findings to prioritize remaining remediation work. Document both the findings and your remediation actions—enterprise buyers will ask for this evidence during vendor security assessments.
Disaster recovery validation. Test your disaster recovery procedures. Actually fail over to your backup systems, measure your actual RTO and RPO, document the results, and update your procedures based on what you learn. Untested disaster recovery is just a document.
Phase 4: Continuous Compliance (Month 10+)
Enterprise readiness isn’t a destination—it’s an operating mode that ensures you pass vendor security assessments continuously.
Continuous monitoring. Implement automated compliance monitoring that continuously validates that your controls remain in place. Configuration drift, access control changes, and policy violations should trigger immediate alerts.
Regular security reviews. Establish a cadence for internal security reviews, external penetration testing, and compliance assessments. Enterprise buyers conducting vendor security assessments will ask when you last conducted these reviews and what you found.
Vendor risk management program. Implement formal processes for evaluating the security posture of your own vendors and third-party dependencies. This closes the irony gap described earlier and demonstrates security maturity.
Quick Wins: Security Controls You Can Implement in 30 Days
While full vendor security assessment readiness takes months, there are meaningful improvements you can make quickly that demonstrate security seriousness to enterprise buyers:
- Enforce MFA across all accounts (days, not weeks)
- Implement a password manager and credential hygiene policy
- Enable audit logging on your cloud infrastructure
- Conduct an access review and revoke unnecessary privileges
- Document your incident response contact list and escalation procedures
- Enable automated vulnerability scanning on your repositories
- Implement a security awareness training program for your team
None of these make you vendor security assessment-ready on their own. But they demonstrate that security is a priority and they reduce your risk profile while you work on the more substantive architectural improvements.
SOC 2, ISO 27001, and Other Certifications: What Actually Matters for Vendor Security Assessments

Understanding the Certification Landscape
The compliance certification landscape is genuinely confusing, and enterprise buyers don’t always make it easier by being specific about what they require in vendor security assessments. Let’s cut through the confusion.
SOC 2 is the baseline for B2B SaaS companies selling to North American enterprise buyers. It’s developed by the AICPA and evaluates your systems against five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. Every enterprise buyer expects you to either have SOC 2 or be actively working toward it when conducting vendor security assessments.
ISO 27001 is the global standard for information security management systems. It’s often required for European enterprise buyers and international conglomerates conducting vendor security assessments. ISO 27001 certification requires establishing, implementing, maintaining, and continually improving a documented information security management system—it’s a more comprehensive organizational commitment than SOC 2.
HIPAA applies if you’re processing protected health information. It’s not optional and it’s not something you can self-certify—your architecture must meet specific technical safeguard requirements that will be validated in vendor security assessments.
PCI DSS applies if you’re processing payment card data. The requirements are prescriptive and specific, and non-compliance carries direct financial penalties.
FedRAMP is required for federal government contracts and is significantly more demanding than commercial enterprise vendor security assessment standards. If you’re targeting government buyers, plan for an 18-24 month FedRAMP authorization process.
SOC 2 Type I vs. Type II: Which Do You Actually Need for Vendor Security Assessments?
This distinction matters more than most startups realize when preparing for vendor security assessments.
SOC 2 Type I is a point-in-time assessment. It validates that your security controls are designed correctly as of a specific date. Getting a Type I report typically takes three to six months from when you start preparing. It’s useful for demonstrating early-stage security commitment in vendor security assessments, but sophisticated enterprise buyers know what it doesn’t prove.
SOC 2 Type II validates that your controls have operated effectively over an extended period—typically six to twelve months. It requires the audit period to begin after your controls are actually in place, which means you can’t rush it. A Type II report is what enterprise buyers actually want to see in vendor security assessments.
The practical implication: if you’re starting from scratch, you’re looking at twelve to eighteen months before you have a SOC 2 Type II report. A Type I report can serve as an interim signal of commitment while you work toward Type II.
One important nuance: SOC 2 is not prescriptive. Unlike PCI DSS, which tells you exactly what controls to implement, SOC 2 evaluates whether your controls are appropriate for your specific system and risk profile. This flexibility is powerful—it means you can design controls that fit your architecture—but it also means there’s no simple checklist that guarantees a clean audit.
When ISO 27001 Becomes Non-Negotiable in Vendor Security Assessments
If more than 30% of your target market is in Europe, or if you’re targeting large multinational corporations, ISO 27001 certification will become a vendor security assessment requirement. The GDPR compliance requirements that come with ISO 27001 certification also address many of the data protection questions that appear in enterprise vendor security assessments.
The key difference between SOC 2 and ISO 27001 is scope. SOC 2 evaluates a specific system or service. ISO 27001 requires implementing an information security management system across your entire organization—policies, processes, people, and technology. It’s a bigger commitment, but it’s also more comprehensive and more globally recognized in vendor security assessments.
Building Audit-Ready Infrastructure from Day One

Architecture Decisions That Enable Vendor Security Assessment Success
The most cost-effective approach to vendor security assessment readiness is building for it from the beginning. The architectural decisions you make in your first year of building will either enable or constrain your ability to serve enterprise customers for the next decade.
Multi-tenancy by design. Build customer data isolation into your data model from the start. Per-customer schema separation is more expensive to implement initially but dramatically less expensive than retrofitting it later. The Citrine Informatics case study from Iterators illustrates this well—their MLOps platform was built with enterprise-grade data isolation from the ground up, enabling them to serve research institutions with stringent data separation requirements without architectural rework.
Zero-trust network architecture. Design your internal network as if it’s already compromised. Every service should authenticate to every other service. No implicit trust based on network location. This architecture is more complex to build initially but dramatically more resilient and much easier to defend during vendor security assessments.
Audit logging as a first-class concern. Build comprehensive audit logging into your application from the beginning. Every significant action—user authentication, data access, configuration changes, administrative actions—should generate structured log entries that can be queried and retained according to compliance requirements. Retrofitting audit logging into an existing application is genuinely painful.
DevOps and Security: Integrating Controls into Your CI/CD Pipeline
The integration of security controls directly into your deployment pipeline is one of the highest-leverage investments you can make for vendor security assessment readiness. It’s also one of the clearest signals of security maturity to enterprise buyers.
A mature security-integrated CI/CD pipeline includes:
- Dependency vulnerability scanning that automatically identifies known vulnerabilities in your third-party dependencies and fails builds that include critical vulnerabilities without documented exceptions.
- Container image scanning that validates the security of your Docker images before deployment, checking for known vulnerabilities in base images and installed packages.
- Static application security testing (SAST) that analyzes your source code for common security vulnerabilities—SQL injection, cross-site scripting, insecure deserialization—before the code reaches production.
- Infrastructure drift detection that continuously validates that your deployed infrastructure matches your Terraform definitions and alerts when unauthorized changes are detected.
- Secrets scanning that prevents credentials from being committed to version control by scanning commits before they’re pushed.
When an enterprise buyer conducting a vendor security assessment asks “how do you prevent insecure code from reaching production?” being able to describe this pipeline in detail—and show them the tooling—is a fundamentally different answer than “our developers are careful.”
Documentation Standards That Pass Vendor Security Assessment Scrutiny
Enterprise auditors conducting vendor security assessments have seen every version of inadequate documentation. They know the difference between a policy that was written to pass an audit and a policy that reflects actual organizational practice.
The documentation that passes enterprise vendor security assessment scrutiny has several characteristics:
It’s specific, not generic. “We encrypt sensitive data” is not a policy. “All customer data is encrypted at rest using AES-256, with encryption keys managed through AWS KMS with automatic rotation every 90 days” is a policy.
It’s current. Documentation that hasn’t been reviewed in two years is worse than no documentation—it suggests that your practices may have drifted from what’s documented without anyone noticing.
It’s cross-referenced. Good security documentation connects policies to procedures to technical controls to evidence. An auditor can follow the chain from “we have an access control policy” to “here’s the policy” to “here’s the procedure for implementing it” to “here’s the evidence that the procedure is followed.”
It’s owned. Every policy and procedure has a named owner who is responsible for keeping it current and enforcing it.
DIY vs. Security Consultants vs. Full-Service Development Partners for Vendor Security Assessment Preparation
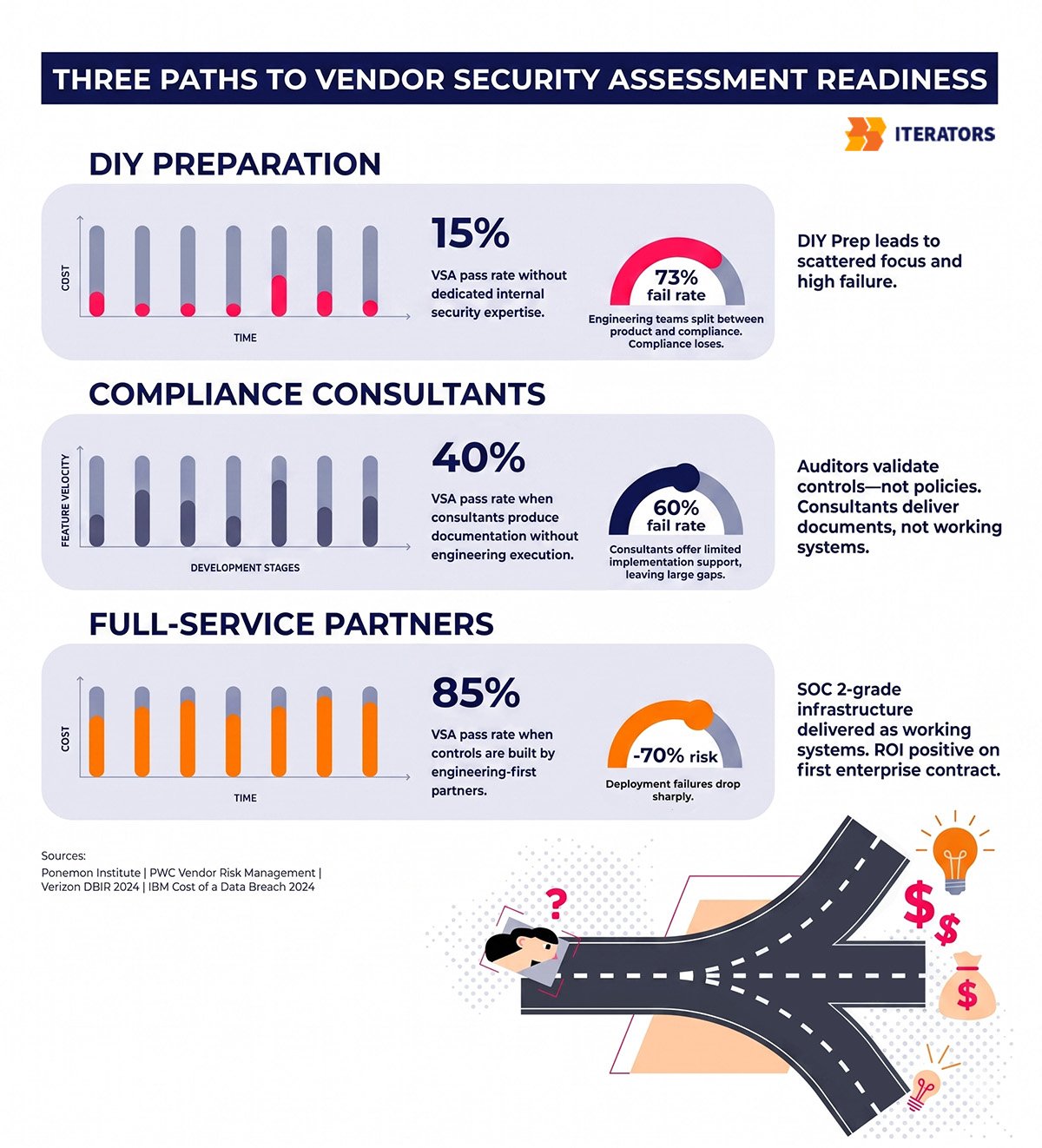
When DIY Vendor Security Assessment Preparation Makes Sense (Spoiler: Rarely)
Let’s be honest about the DIY option for vendor security assessment preparation. If you have a mature security team with enterprise compliance experience, and you have the engineering bandwidth to do the architectural work alongside your product roadmap, DIY enterprise readiness is possible.
Most early-stage SaaS startups have neither of these things.
The typical startup security team is one or two engineers who are also responsible for infrastructure, DevOps, and keeping the product running. Asking them to also drive a SOC 2 Type II certification while building enterprise-grade multi-tenancy while maintaining the existing product is a recipe for burnout, corners being cut, and an audit that reveals the shortcuts.
The other DIY challenge is expertise. Vendor security assessment requirements are complex and specific. Getting them wrong—implementing controls that look right but don’t actually satisfy the requirements—wastes months of work and results in audit failures that are more damaging than not having attempted the certification at all.
The Consultant Trap: Why Advice Without Implementation Often Fails Vendor Security Assessments
The compliance consulting industry has a fundamental business model problem: they get paid for advice, not outcomes. A consultant can tell you that you need Vault-backed secrets management, document a policy for it, and mark the control as “designed” in your SOC 2 readiness assessment. But if the engineering work to actually implement it doesn’t happen, you’ll fail the vendor security assessment.
This is the pattern that Jacek Głodek describes directly: “AI consulting is mostly slides. We’re not consultants. We build. There’s a huge difference between telling someone how LLMs might help them versus delivering a production-grade system with observability, versioning, safety nets, and fallback strategies.”
The same principle applies to security consulting for vendor security assessments. The gap between a well-written security policy and a functioning security control is an engineering problem. Consultants who produce documentation without implementation deliverables are solving the wrong problem.
How Full-Service Partners Accelerate Vendor Security Assessment Readiness
The most effective approach for most SaaS startups preparing for vendor security assessments is a full-service technical partner who combines security expertise with engineering execution.
This isn’t just about having someone to write your policies—it’s about having engineering teams who build enterprise-grade infrastructure, understand compliance requirements, and embed security controls into product architecture from the beginning.
The Iterators approach to vendor security assessment preparation is explicitly engineering-first. As described in the SaaS development methodology: “Implement SOC 2-grade controls and enterprise security practices that pass vendor assessments and security reviews. Our security implementation includes Vault-backed secrets management, encrypted backups with audit trails, hardened jump-host configurations, and image scanning in CI/CD pipelines. These aren’t theoretical security measures—they’re practical implementations that enable enterprise sales cycles and regulatory compliance.”
The Imperative case study illustrates what this looks like in practice. Over nine years of partnership, Iterators built and maintained a peer coaching platform that serves Fortune 500 companies including Zillow, Hasbro, and Boston Scientific. The platform required enterprise-grade SOC 2 compliance, complex organizational hierarchy management, and security controls that satisfied procurement requirements at some of the world’s most security-conscious organizations. The result: over $7 million in revenue generated, with security architecture that enabled rather than blocked enterprise sales.
ROI Analysis: Proactive Investment vs. Reactive Compliance for Vendor Security Assessments
The financial case for investing in vendor security assessment readiness before you have enterprise customers is straightforward once you run the numbers.
Proactive investment: Six to twelve months of engineering work, compliance tooling costs, and external audit fees. Typically $150K to $400K depending on the scope of architectural changes required and whether you’re using an internal team, external consultants, or a full-service partner.
Reactive compliance (after failing a vendor security assessment): The cost of the lost deal (let’s say $200K ARR), the sales cycle waste (three to six months of enterprise sales team time), the engineering cost of retrofitting security (often higher than proactive investment because you’re working against existing architecture), and the delay in being able to close subsequent enterprise deals.
The math consistently favors proactive investment. And this doesn’t account for the compounding advantage of being vendor security assessment-ready before your competitors—the deals you close that they can’t, the market positioning you establish, and the enterprise references you build.
Frequently Asked Questions About Vendor Security Assessments

How long does it take to prepare for a vendor security assessment?
It depends on where you’re starting from. If your infrastructure is reasonably mature and you have basic security hygiene in place, you can prepare for a SIG Lite vendor security assessment in two to four weeks. A deep-dive SIG Core or SOC 2 Type II audit requires six to eighteen months of preparation, depending on the current state of your architecture and documentation.
What’s the minimum security baseline for enterprise vendor security assessments?
At minimum: MFA enforcement across all accounts, data encrypted at rest and in transit, documented incident response plan, access control policy with regular reviews, and basic security monitoring. This gets you through the door for initial conversations, but won’t pass a rigorous deep-dive vendor security assessment.
Do we need SOC 2 before pursuing enterprise deals?
Not necessarily, but you need to be actively pursuing it. Many enterprise buyers conducting vendor security assessments will accept a SOC 2 Type I report or a documented roadmap toward Type II as an interim measure. What they won’t accept is no plan at all.
How much does vendor security assessment preparation actually cost?
Expect $150K to $400K for the engineering work, tooling, and audit fees, depending on your starting point and the scope of changes required. This is a one-time investment that enables ongoing enterprise revenue—the ROI is typically positive within the first enterprise deal closed.
Can we pass vendor security assessments without formal certifications?
For some enterprise buyers, yes. Self-attestation with strong supporting documentation can satisfy lower-risk vendor reviews. For critical infrastructure vendors or buyers with stringent procurement requirements, independent certification is typically required for vendor security assessments.
What happens if we fail a vendor security assessment?
The deal typically pauses or terminates. In the best case, the buyer gives you a remediation list and a timeline to resubmit. In the worst case, they move to a competitor. The reputational impact within the buyer’s organization and procurement network can also affect future vendor security assessment opportunities.
How do we prioritize security investments with limited budget for vendor security assessments?
Focus on the controls that appear most frequently in enterprise questionnaires and that represent the highest actual risk: secrets management, MFA enforcement, data encryption, access control documentation, and incident response planning. These five areas cover the majority of common vendor security assessment failures.
When should we start preparing for enterprise vendor security assessments?
The honest answer is: before you have enterprise customers. The ideal time to start building enterprise-ready infrastructure is when you’re building your initial architecture. The second-best time is now.
Conclusion: Vendor Security Assessment Readiness Is an Engineering Problem, Not a Paperwork Problem
The 73% failure rate of SaaS startups in vendor security assessments isn’t a mystery. It’s the predictable result of treating enterprise security as an administrative challenge—something to document your way through—rather than an engineering challenge that requires building the right infrastructure.
Fortune 500 buyers conducting vendor security assessments aren’t fooled by polished questionnaire responses. They’re looking at your architecture, your controls, and your evidence. They’re asking whether your infrastructure can actually protect their data, not whether you have a policy that says it will.
The startups that win enterprise deals consistently are the ones who made the decision to build for vendor security assessment readiness early—before the pressure of a specific deal, before the six-month sales cycle, before the questionnaire landed. They treated security architecture as a product decision, not a compliance checkbox.
If you’re reading this because a deal just died in vendor security assessment review, the path forward is clear: stop treating the symptom (the failed assessment) and fix the cause (the architecture that couldn’t pass it). That requires engineering work, not better documentation.
If you’re reading this because you’re planning ahead, you’re already ahead of most of your competitors. Use that advantage.
At Iterators, we’ve helped startups navigate this exact challenge—building the enterprise-grade infrastructure that passes rigorous vendor security assessments and enables the enterprise sales cycles that transform companies. We don’t produce slide decks about what you should build. We build it.
Don’t let your next enterprise deal die in vendor security assessment. Schedule a free consultation with Iterators to assess your current security posture, identify the gaps that would fail a vendor security assessment, and build the infrastructure that closes them.
