Imagine this: you’ve just bought the latest smartphone with all its cutting-edge features and are excited about its possibilities. But when you connect it to your company’s outdated database or software, it’s like trying to fit a square peg into a round hole. It’s the essence of legacy tech, where the past refuses to yield to the future.
Like many others, your business may be seeking ways to balance the allure of innovation and the shackles of the past.
Keeping pace with evolving technology while grappling with legacy systems leaves them stuck in a different era. Legacy technologies, data, and code are the ballast holding back the ship of progress, but in this article, we’ll show you how to navigate these waters and steer your business toward the shores of modernization.
Characteristics of Legacy Tech, Data, and Code
Legacy technology, data, and code are the digital footprints of years ago that continue to shape today’s business landscape. Recognizing their common characteristics is crucial to understand their impact and challenges. Here’s a comprehensive look at what defines legacy systems.
- Outdated Technology: At the heart of legacy systems lies technology that has seen better days. These systems often run on outdated hardware, software, or both. It’s like driving a classic car; it has charm, but it could be more fuel-efficient and equipped with modern safety features.
- Lack of Integration: One of the most glaring issues with legacy tech is its inability to integrate with contemporary systems seamlessly. It’s like trying to connect a VHS player to a smart TV – the compatibility issues are glaring. This lack of integration hampers data flow and can lead to inefficiencies.
- Costly Maintenance: Legacy systems require continuous care and attention. Like vintage cars, they demand specialized maintenance that can be costly. It includes finding experts who understand the obsolete technology and ensuring spare parts or software updates are available.
- Security Vulnerabilities: Cyber threats evolve rapidly, but legacy systems are stuck in time. Their outdated security features can make them easy targets for hackers. It’s like trying to secure an old fortress with modern weapons pointed at it.
- Inflexibility: Legacy systems often operate on rigid structures. They’re like old buildings with immovable walls. Making changes or updates can be cumbersome and expensive, hindering adaptability in a rapidly changing business environment.
- Limited Support: Over time, the companies that created these legacy systems may cease to exist, leaving users needing support. It’s like buying a product from a company that no longer exists – you’re on your own when issues arise.
- Data Silos: Data is the lifeblood of modern business, but legacy systems often store data in isolated silos. Extracting and sharing this data with other systems can be a major challenge, hindering decision-making and analytics.
- User Resistance: Users become accustomed to the quirks and limitations of legacy systems, making them resistant to change. It’s like trying to convince someone to switch from their old flip phone to a modern one.
- Slow Performance: As technology advances, the gap between legacy and contemporary systems widens. Legacy systems often need help to keep up with the speed and efficiency expected in today’s fast-paced business environment.
- Compliance Risks: Regulatory requirements evolve, but legacy systems may still need to. It poses a risk for businesses as they might fail to meet compliance standards, potentially resulting in legal issues.
- Limited Vendor Support: Even if vendors still exist, they may need to provide support or updates for their older products. It can leave businesses hanging when they need assistance or encounter issues.
- Reduced Innovation: Legacy systems hinder a company’s ability to innovate. They’re like a ball and chain, slowing progress and preventing businesses from staying competitive.
Understanding these common characteristics is the first step in addressing the challenges posed by legacy technology, data, and code. In the following sections, we’ll explore strategies to mitigate these issues and guide you toward making informed decisions about the future of your technology landscape.
Legacy Tech vs. Modern Solutions
The goal of making informed decisions about legacy technology makes it necessary to grasp the distinctions between these older systems and their modern counterparts. The differences are stark, and understanding them is crucial to evaluating the need for an upgrade.
| Legacy Technology | Modern Solutions | |
| Architecture | Legacy technology often features rigid, monolithic architectures that are challenging to modify. | Modern technology relies on scalable and flexible architectures that adapt to changing needs. |
| Integration | Legacy technology struggles in this regard, leading to data silos and inefficient operations. | Modern technology prioritizes seamless integration, allowing data to flow effortlessly between systems. |
| User Experience | Legacy systems, designed in a different era, often need these user-centric features. | Modern software and applications emphasize user-friendliness, intuitive interfaces, and accessibility. |
| Security | Legacy systems may have vulnerabilities that make them appealing targets for cyberattackers. | Modern solutions incorporate the latest security measures because security is paramount in today’s digital landscape. |
| Scalability | Legacy systems may require substantial overhauls to accommodate growth. | As businesses grow, their technology needs to scale with them. Modern solutions can expand easily to accommodate new business needs. |
| Cost | Legacy systems can be expensive to maintain and support due to their outdated nature. | Modern solutions often offer more cost-effective and efficient operations. |
| Speed | Legacy systems may need help to cope in the modern business environment. | Modern systems prioritize speed and efficiency, making them suitable for today’s fast-paced business environment where speed is essential. |
| Data Management | Legacy systems often lag in this department, creating data silos and limiting data-driven decision-making. | Modern solutions excel in data management, providing tools for analytics and real-time insights. |
| Compliance | Keeping up with evolving compliance standards is critical. Legacy systems may lack the necessary updates to fulfill emerging compliance standards. | Modern solutions typically offer features that help companies remain compliant |
| Innovation | Legacy systems can stifle innovation due to their inflexibility. | Modern technology enables innovation and adaptation to market changes. |
| Support | Legacy systems may need more support and a dwindling user base. | Modern solutions benefit from robust vendor support, regular updates, and a community of users. |
| Adaptability | Legacy systems can resist change and may need help to keep up with emerging technologies. | Modern solutions are built to adapt to new technologies and trends. |
Recognizing these distinctions between legacy technology and modern solutions underscores the necessity of addressing the limitations of legacy systems. In the subsequent sections, we’ll explore strategies for addressing these challenges and guiding your business toward a more agile and efficient technological landscape.
Benefits and Drawbacks of Maintaining Legacy Tech

Maintaining legacy systems is a complex decision. It comes with potential benefits and significant drawbacks, and businesses must carefully consider these factors before deciding to keep their older technology, data, and code.
The Benefits
Here are some benefits of maintaining your current tech systems:
- Cost Efficiency: Initially, maintaining legacy systems can be cost-effective. There’s no need for a major investment in new technology, and businesses can continue using existing resources.
- Minimal Disruption: Upgrading or replacing systems can cause downtime and disruptions. Legacy systems, in contrast, can continue operating while you evaluate other options.
- Familiarity: Employees are often accustomed to legacy systems, which can reduce training and transition time. This familiarity can result in higher productivity, at least in the short term.
- Data Retention: Legacy systems hold historical data, which can be valuable for historical analysis or compliance purposes.
The Drawbacks
Here are some issues you may encounter when maintaining legacy tech systems:
- Limited Functionality: Legacy systems need more modern features and capabilities, hindering your ability to compete and innovate in a fast-evolving market.
- Security Risks: Outdated technology often has vulnerabilities that cybercriminals can exploit, potentially resulting in data breaches or other security incidents.
- Reduced Productivity: Legacy systems must integrate better with newer software and hardware, causing inefficiencies and hampering overall productivity.
- Maintenance Costs: Over time, the cost of maintaining and supporting legacy systems can become prohibitive. Finding skilled personnel who understand older technology can take time and effort.
- Compliance Challenges: Legacy systems may not meet evolving regulations, leaving your business at risk of non-compliance and potential legal consequences.
- Inflexibility: The rigidity of legacy systems can stifle your business’s adaptability and ability to respond to changing market conditions or opportunities.
- Competitive Disadvantage: Businesses that rely on legacy systems may need help to keep up with competitors who have embraced modern technology, potentially losing market share.
- Vendor Discontinuation: Vendors may discontinue support for legacy systems, leaving you without critical updates and security patches.
- Data Silos: Legacy systems often create data silos, making it challenging to access and utilize data effectively for decision-making.
- Long-term Viability: The question of how long your legacy systems can continue to function without causing major disruptions is still being determined, leading to concerns about long-term viability.
In assessing whether to maintain legacy systems, businesses must weigh these benefits against the drawbacks. It’s a delicate balance between the familiarity and initial cost savings that legacy systems offer and the need to adapt, innovate, and secure their digital future. Ultimately, the decision hinges on an organization’s specific needs, goals, and the nature of its industry. In the following sections, we’ll explore strategies for addressing these challenges, providing you with the information needed to make an informed decision.
Challenges Working with Legacy Code

Businesses often encounter unique challenges when working with legacy code and aiming to build additional modules or functionalities. While the desire to expand or improve existing systems is natural, it’s important to recognize and address potential obstacles.
- Compatibility Issues: The older code may not be compatible with modern development tools, frameworks, or libraries, making the process complex and error-prone.
- Lack of Documentation: Legacy code often needs more adequate documentation, so developers may need to decipher the code’s logic, structure, and dependencies. It can be time-consuming and error-prone, leading to delays.
- Technical Debt: Building new modules on top of legacy code can accumulate technical debt. It’s the metaphorical interest you pay on the decisions made in the past, which can impede future development and maintenance.
- Maintainability Challenges: Over time, the cost of maintaining and supporting legacy systems can become prohibitive. Finding skilled personnel who understand older technology can take time and effort.
- Testing Complexities: Properly testing new modules within the context of legacy systems can be challenging. The lack of documentation and the interconnectedness of components can make it hard to ensure comprehensive test coverage.
- Performance Issues: Legacy systems need to have the performance capabilities required for modern applications. As a result, new modules may need to improve, leading to user satisfaction.
- Security Concerns: Building new modules on top of legacy code often demands more time and resources than developing from scratch. It’s like trying to renovate an old building rather than constructing a new one.
- Resource Drain: The lack of scalability in legacy systems can restrict the growth and adaptability of the new modules. It’s like attempting to build a skyscraper on an unstable foundation.
- Limited Scalability: Developers working on the project may have to acquire specialized knowledge about outdated technologies, adding to the learning curve and potentially resulting in errors.
- Knowledge Gaps: The question of how long your legacy systems can continue to function without causing major disruptions is still being determined, leading to concerns about long-term viability.
In order to address these challenges, businesses must take a strategic approach. It might involve gradually refactoring legacy code to make it more adaptable, incorporating modern development practices, and investing in robust testing and documentation. A complete overhaul might be necessary in some cases, migrating to a more contemporary system while salvaging valuable data and insights from the legacy code. It’s a decision that a thorough analysis of the organization’s specific needs, goals, and constraints should guide.
Navigating the complexities of working with legacy code while building additional modules can be demanding. Still, with the right strategies and a clear understanding of the challenges, businesses can find ways to modernize and enhance their technology landscape.
Managing Complexities of Legacy Tech

In organizations dealing with millions of lines of outdated code and databases, managing the complexities of legacy systems is a formidable task. These systems often present unique challenges and demand careful planning to ensure they continue to serve the organization’s needs.
7 Ways to Manage Large Legacy Codebases
Dealing with massive legacy codebases can be akin to sorting through an extensive archive without a catalog. To streamline maintenance and improve efficiency, consider the following strategies:
- Prioritization: Not all parts of the codebase are equally critical. Identify core components that require immediate attention, especially those that impact security or compliance.
- Modularization: Break the code into manageable modules. This approach lets developers focus on one component at a time, making maintenance and updates more straightforward.
- Refactoring: Refactoring involves reorganizing and improving code without altering its external behavior. This process can make the code more maintainable and less error-prone.
- Documentation: As you work through the code, document your findings and changes. Over time, this documentation will become invaluable for understanding and maintaining the codebase.
- Testing: Develop a robust testing strategy. Automated testing can help identify issues and prevent regressions as you change the code.
- Training and Knowledge Transfer: Ensure your team has the skills and knowledge to work with the code. Encourage knowledge sharing and consider mentorship programs.
- Version Control: Implement version control systems to track changes and manage code collaboration efficiently.
5 Effects of Old Databases on Data Handling in Modern Apps
Outdated databases within legacy systems can severely impact an organization’s data management and integration capabilities. These databases often suffer from the following issues:
- Data Inefficiency: Outdated databases may store data inefficiently, leading to slower data retrieval and storage operations. It can hinder the performance of modern applications.
- Limited Data Types: Older databases may need more support for contemporary data types, making it challenging to manage new data generated by modern applications.
- Integration Hurdles: Integrating outdated databases with modern applications can be complex. Data may need to be transformed and adapted to meet the requirements of the new software.
- Scalability Concerns: Outdated databases may need to scale to handle large volumes of data generated by modern applications. It can result in bottlenecks and reduced efficiency.
- Security Risks: Older databases may have known vulnerabilities that are no longer patched. It can expose sensitive data to security risks such as DDoS (Distributed Denial of Service) and Man-in-the-Middle attacks.
Risks of Maintaining Extensive Code without Proper Documentation
Maintaining extensive code without proper documentation is akin to navigating a labyrinth without a map. The risks are substantial and include:
- Knowledge Loss: Over time, knowledge about the codebase may be lost as team members change or retire. With documentation, understanding the code becomes easier.
- Maintenance Delays: With documentation, diagnosing and fixing issues can be faster, resulting in delayed maintenance and potentially longer system downtime.
- Increased Error Rates: Undocumented code is more susceptible to errors and bugs. Developers may inadvertently introduce issues while working with poorly documented code.
- Onboarding Challenges: New team members face steep learning curves when understanding extensive, undocumented codebases. It can hinder the integration of new talent.
- Compliance Risks: In regulated industries, lack of documentation can lead to compliance issues, which can have serious legal and financial consequences.
Managing extensive codebases and databases in legacy systems demands a strategic approach. Prioritization, modularization, documentation, and refactoring are key strategies to improve maintainability. Additionally, understanding the impact of outdated databases on data storage, retrieval, and integration is crucial for modernizing your technology stack. Proper documentation safeguards against the risks of knowledge loss, delays, errors, and compliance issues that come with maintaining extensive code without clear guidance.
Manual Server Configurations
Manual server configurations entail the process of setting up and adjusting server settings, parameters, and options by human intervention, without the assistance of automated tools or scripts. This approach introduces a spectrum of challenges, giving rise to various issues that impact the effective management of complex legacy systems. The reliance on manual configurations heightens the risk of errors, leading to inconsistencies in server setups and potentially resulting in system downtimes, performance bottlenecks, and increased vulnerability to security threats.
Also, manual configurations often lack the scalability required to adapt to the needs of modern technologies. As the complexity of legacy systems grows, managing and updating configurations becomes an arduous task, hindering agility and responsiveness to changes.
Inefficient resource allocation is another fallout of manual server configurations within legacy systems. Without automated processes, it becomes challenging to optimize resource utilization, leading to increased operational costs and diminished overall system efficiency.
So, what’s the solution? Automated configuration management tools are the answer. They simplify the process, amp up accuracy, and make scalability a breeze. It’s like turning on the easy mode for dealing with manual server configurations, helping us stay strong against the challenges of modern tech demands.
Legacy Integrations and Interfaces

Organizations dealing with legacy integrations and interfaces face unique challenges. The intricacies of integrating old and new systems can be both daunting and rewarding, demanding a nuanced approach. Let’s explore the complexities and strategies involved in this intricate process.
Understanding Legacy Integrations
Before delving into the challenges, it’s essential to understand what legacy integrations entail. These connections and bridges between older systems are often developed at different times with varying technologies and protocols. These integrations are the arteries through which data and processes flow. The complexity arises when the technology and standards used in these integrations no longer align with modern counterparts.
Compatibility
One of the foremost challenges in dealing with legacy integrations is ensuring compatibility between older systems and contemporary technology. It often involves issues like data format incompatibility, where legacy systems may use outdated data formats that modern systems need help interpreting, resulting in data loss or corruption during integration. Additionally, communication protocol mismatch may occur, as legacy systems rely on outdated communication protocols, making it challenging to connect with modern applications. Inflexible interfaces in older systems can be rigid and need more flexibility to adapt to the dynamic needs of modern applications.
Security
Security is a paramount concern when dealing with legacy integrations. Legacy systems may need the robust security features and encryption standards expected in contemporary technology. It can pose risks such as data breaches due to weak security measures, making legacy systems susceptible to unauthorized access. Moreover, organizations might struggle to meet compliance standards because of the lack of modern security features in their legacy integrations, potentially leading to legal consequences.
Scalability and Performance
Legacy integrations can hinder scalability and performance, particularly when connecting older systems to high-demand modern applications. Issues include scalability limits, as older systems might need to scale better to accommodate increased data flows and transactions, resulting in performance bottlenecks. Furthermore, the time it takes for data to travel between systems can increase latency and lead to slower response times, affecting user experience.
Maintainability and Documentation
Maintaining legacy integrations becomes increasingly challenging when there’s insufficient documentation. With time, knowledge about the intricacies of these integrations can be lost, and developers might need help understanding or modifying them. Insufficient documentation can lead to extended downtime when issues arise, causing extended periods of system downtime. Developers may inadvertently introduce errors while working with legacy integrations without proper documentation.
Legacy and Modern Systems Coexistence
In a transitional phase, organizations often need to maintain a balance between legacy and modern systems. Integrations should facilitate this coexistence while minimizing disruption. Challenges include ensuring data flows smoothly between legacy and modern systems while synchronizing data and maintaining a seamless user experience across integrated systems.
Addressing these complexities involves a combination of strategies, including modernizing legacy systems, implementing secure integration protocols, providing comprehensive documentation, and planning for gradual transitions to reduce disruption. Dealing with legacy integrations and interfaces is undoubtedly intricate, but the right approach can pave the way for more efficient, secure, and adaptable technology ecosystems.
Scarcity of Developers Skilled in Legacy Tech
As the tech industry charges forward with ever-evolving stacks and languages, organizations still reliant on legacy systems face a growing challenge: the need for more developers proficient in older tech stacks. This scarcity can have far-reaching consequences and lead to difficult decisions.
The consequences of relying on a dwindling pool of developers skilled in legacy technologies are manifold. First and foremost, it can lead to:
- Increased Maintenance Costs: With fewer developers proficient in legacy systems, the cost of hiring or retaining such talent often skyrockets. The need for more experts in older tech stacks translates to premium salaries.
- Extended Project Timelines: Scarcity results in delays. Projects reliant on legacy systems take longer to complete, leading to a backlog of work and a slower pace of innovation.
- Knowledge Gaps and Errors: The need for skilled developers can result in knowledge gaps and errors. Mistakes and oversights are more likely, leading to inefficiencies and costly corrections.
- Reduced Innovation: Stuck in a cycle of maintaining outdated technology, organizations need help to allocate resources for innovation and strategic growth.
Cost of Hiring Developers for Legacy Tech
The decision of whether to hire developers to maintain legacy systems or to embark on migration to modern technology is pivotal. It’s a choice between sustaining the status quo or catalyzing a transformation. It’s where we introduce Iterators. We’re a software company with a track record of helping companies deploy modern tech securely.
Iterators’ team of developers excels in Scala, a modern and scalable enterprise language. Their proficiency extends not only to this language but also to legacy technologies, bridging the gap between the old and the new.
By collaborating with Iterators, businesses can reap the following benefits:
- Cost-Efficiency: The highly experienced team at Iterators provides a cost-effective solution to the scarcity of legacy developers. Their expertise enables streamlined maintenance, reducing labor costs.
- Reduced Timelines: With Iterators, projects progress swiftly. Their proficiency in modern languages and legacy systems ensures quicker project delivery.
- Innovation Acceleration: Free from the constraints of legacy systems, businesses can redirect resources towards innovation, enhancing competitiveness and market adaptability.
- Security and Scalability: Iterators’ developers prioritize security and scalability, guaranteeing a smooth transition from legacy systems to modern technology.
- Reduced Error Rates: By working with a skilled team, organizations can expect fewer errors, improved efficiency, and reduced costly corrections.
The future belongs to those who can adapt swiftly and securely, and Iterators empower organizations to transition from legacy technology to modern solutions. The decision is no longer between scarcity and stagnation; it’s between embracing a dynamic future and remaining trapped in the past. It’s a choice that opens the doors to innovation and profitability.
However, in situations where retaining legacy tech is in your best interest, short-term and long-term, you need to be able to have trusted developers to ensure your business runs smoothly. Therefore,it’s time to partner with Iterators to avail your operations of seasoned legacy stack engineers. They’ll keep your enterprise systems scalable, reliable, and robust in the face of modern consumer demand, ultimately redefining your technological landscape.
Unmanageable Legacy Code

Unmanageable legacy code presents organizations with a labyrinth of complexities. Balancing the need to maintain these systems while modernizing their tech stack is a formidable task that demands a strategic and collaborative approach. In this section, we explore strategies to tackle unmanageable legacy code while embracing the concept of shared responsibility in decision-making.
Strategies to Maintain Legacy Systems while Modernizing Tech Stack
To effectively manage unmanageable legacy code, organizations can employ several key strategies:
- Incremental Refactoring: Break down the codebase into smaller, manageable segments for gradual refactoring and modernization, reducing the risk of disruption.
- Integration Layer: Implement an integration layer that acts as a bridge between legacy and modern systems, ensuring data flow and functionality while preserving legacy investments.
- Containerization and Microservices: Containerization and microservices enable the gradual replacement of legacy components with modern, scalable, and independent services, improving agility.
- Documentation and Knowledge Transfer: Invest in comprehensive documentation and knowledge transfer to bridge the knowledge gap and facilitate smoother transitions.
- Testing and Quality Assurance: Rigorous testing and quality assurance procedures are essential to identify and mitigate issues in the legacy codebase.
The concept of being responsible for aspects you can’t take ownership or accountability of introduces complexities into the decision-making process, particularly in the context of unmanageable legacy code. It implies a shared responsibility and collaborative approach, which can be challenging to implement.
Lack of ownership affects decision-making in the following ways:
- Collaborative Decision-Making: When no single individual or team can take full ownership of legacy code, decisions become a collaborative effort. This can lead to slower decision-making processes as multiple stakeholders must be consulted and consensus reached.
- Risk Management: The shared responsibility model encourages a cautious approach to decision-making, with a strong focus on risk assessment and mitigation. It may result in more conservative decisions to avoid potential pitfalls.
- Resource Allocation: The concept necessitates careful resource allocation. Decision-makers must consider how to distribute resources effectively among various teams responsible for different components of the legacy code.
- Communication and Transparency: Effective communication and transparency are critical in a shared responsibility model. Decision-makers must ensure that all stakeholders are informed and aligned, which can be time-consuming.
- Innovation and Modernization: The shared responsibility model can slow down the adoption of innovative solutions or modernization efforts, as consensus and alignment among multiple stakeholders can take time.
Despite its challenges, this concept also brings the benefits of diversity of perspectives, shared problem-solving, and a more comprehensive approach to decision-making. It encourages organizations to build a culture of collaboration, adaptability, and accountability.
Navigating the complexities of being responsible for aspects you cannot fully own or control requires a careful balance of teamwork, communication, and strategic decision-making. It’s an approach that acknowledges the intricacies of modernizing legacy systems while preserving existing investments and knowledge.
Reproducible Development Environments and Understanding of System Flow
Organizations in a fast-paced technological landscape often need more reproducible development environments and a comprehensive understanding of system flow. These challenges can cast a shadow on efficiency, security, and overall progress. Let’s delve into the intricacies of these issues.
Ensuring Consistency in Reproducible Development Environments
Reproducible development environments are the bedrock of software development. They ensure consistency, predictability, and reliability throughout the development lifecycle. However, the absence of such environments introduces many challenges that can hamper the development process.
- Inconsistent Testing: A lack of reproducible environments can result in inconsistent testing outcomes. Developers may need to be more consistent with their local development setups and the production environment, making identifying and rectifying issues difficult. This inconsistency can lead to delayed releases, increased debugging time, and compromised software quality.
- Dependency Conflicts: Inconsistent development environments often lead to dependency conflicts. These conflicts can arise when different team members use distinct versions of libraries, frameworks, or other dependencies. As a result, code may behave differently across environments, making code deployment and operation more complex. Managing dependencies becomes challenging, requiring additional effort and leading to potential errors and delays.
- Difficulty in Collaboration: Effective collaboration is a cornerstone of successful software development. When developers work in disparate, unreproducible environments, it becomes challenging to maintain synchronization and alignment within the team. Inconsistencies can lead to miscommunication, misunderstandings, and difficulties in coordinating tasks. This lack of cohesion can hinder the collective progress of the development project.
Strategies for Building Reproducible Development Environments
To address the challenges related to reproducible development environments, organizations can implement several strategies:
- Containerization with Docker: Adopt containerization technologies like Docker to encapsulate applications and their dependencies. This ensures consistent environments across different stages of the development process, from local development to production.
- Version Control with Git: Embrace version control systems such as Git to manage code and configurations. Version control helps maintain a consistent codebase, facilitates collaboration, and allows for the reproducibility of development environments.
- Infrastructure as Code (IaC): Implement IaC tools like Terraform or Ansible to define and provision infrastructure. IaC ensures that the underlying infrastructure is consistent and reproducible, supporting development efforts.
Understanding System Flow
A comprehensive understanding of system flow is essential for efficient software development and maintenance. It involves visualizing the sequence of interactions, data flow, and dependencies within a software system. However, when organizations need this understanding, they encounter various challenges.
- Inefficient Troubleshooting: Troubleshooting issues becomes an arduous and time-consuming process without a clear system flow map. Developers may need help to pinpoint the source of problems, leading to extended downtime and reduced system availability.
- Suboptimal Resource Allocation: A lack of comprehensive system flow knowledge can result in suboptimal resource allocation. Organizations may invest resources in areas of the system that do not contribute to overall efficiency or performance. This misallocation of resources can lead to inefficiencies, wasted investments, and delays in project delivery.
- Security Vulnerabilities: Incomplete knowledge of system flow can result in undetected security vulnerabilities. With a clear understanding of how data and processes interact, organizations may notice potential weak points in the system. Malicious actors can exploit these vulnerabilities, leading to security breaches and data loss.
Benefits of Visualizing System Flow
Organizations can benefit from visualizing system flow to overcome the challenges related to understanding system flow. This approach offers several advantages:
- Efficient Troubleshooting: Visualizing system flow provides a clear and intuitive way to trace data and process interactions. When issues arise, troubleshooting becomes more efficient, as developers can quickly identify the source of problems and implement targeted solutions.
- Optimized Resource Allocation: A visual representation of system flow helps organizations identify critical components and areas that require attention. This knowledge enables organizations to allocate resources judiciously, investing in areas that contribute to overall efficiency and performance.
- Enhanced Security: Visualizing system flow allows organizations to identify potential security vulnerabilities and weak points in the system’s architecture. By proactively addressing these issues, organizations can enhance security and minimize the risk of breaches.
In software development, the challenges of unmanageable legacy code can be addressed through strategic approaches. By embracing reproducible development environments and gaining a comprehensive understanding of system flow, organizations can navigate complexities, enhance efficiency, and secure the success of their development projects.
Value of Introducing Proper Documentation in Legacy Systems

Effective documentation is an invaluable asset for legacy systems. It illuminates the inner workings of aging software, making it understandable and manageable for current and future developers.
To document legacy applications effectively, organizations should use:
- Comprehensive Annotations: Annotate code, providing explanations for functions, variables, and modules. It improves understanding of the software’s functionality.
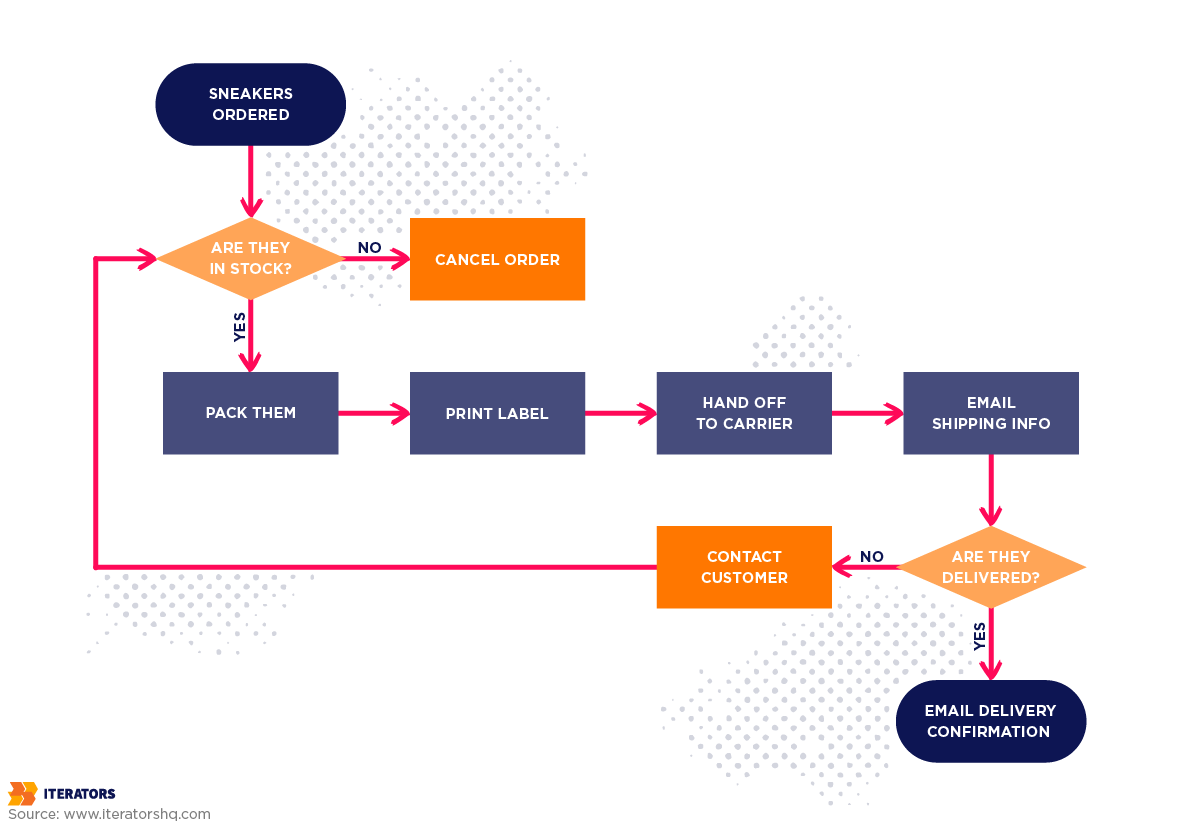
- Flowcharts and Diagrams: Visual representations, like flowcharts and diagrams, help elucidate the structure and logic of legacy systems.
- Version Control: Use version control systems to track code changes and provide insights into historical modifications and decisions.
In a legacy context, we recommend you follow these best practices for documentation:
- Structured Documentation: Organize documentation into sections, covering code, tech stacks, and environment setup. This makes information easily accessible.
- Updated Records: Keep documentation up-to-date, reflecting changes and adaptations in the legacy system.
- Clear Naming Conventions: To facilitate comprehension, use clear and consistent naming conventions for code, files, and documentation.
Navigating the Legacy Landscape with Confidence
Legacy systems, data, and code pose challenges and opportunities. As we’ve covered in this comprehensive guide, the journey begins with understanding the common characteristics of legacy tech, differentiating them from modern solutions, and recognizing the benefits and drawbacks of maintenance. Challenges emerge when dealing with legacy code, working on additional modules, managing complex databases, and facing manual server configurations. However, each hurdle can be surmounted with thoughtful strategies and collaborations.
The scarcity of developers skilled in legacy technology is a reality, but organizations can embrace a future powered by modern tech, with Iterators as their reliable process optimization partner.
From managing legacy integrations and interfaces to dealing with unmanageable code, Iterators offer a way forward. Now is the time to unlock the potential of legacy systems and transition confidently to modern technology. Discover a path forward, embrace innovation, and partner with Iterators to rewrite your technology story.
